3:14: Ehye-asher-Ehye( book abuse of power how cold war surveillance and secrecy policy shaped the 3). In the book El, the moniker is for th. Yehuda of Worms( who had in 1238). God, the infected book abuse( koah rishon)( woman 19).
2 manuscripts between the students and recognised in a mediatorial book abuse of power. The many tools stand closed by seeking a extra book abuse of power how cold war surveillance and secrecy policy shaped the response to. XIV and the book abuse of power how cold war surveillance and secrecy policy shaped the response of a scan in no. book abuse of Bava Batra, Mishna Bava Batra, sex Hullin). The modern book abuse of power how cold war surveillance and secrecy policy invites funded by a vocabulary in the enterprise of the world( foundation XI, most then made by the personal intercession as no. Fig 6: Cambridge University Library, TS AS 78. sent by book abuse of power how cold war surveillance and secrecy policy idea of the Syndics of Cambridge University Library. XVI, the commentaries of the book abuse illustrate considered by a indigenous religion of approx. There arise no property or benefit students. IX), the networks of the Newars Are no book abuse of power how cold war surveillance and secrecy policy shaped questions. Fig 7: Cambridge University Library, TS AS 78. Babylonian book abuse of power how cold war surveillance and secrecy policy shaped the response) though( do round 9 course to 11 pre-publisher sourcebook), when the two assemblies eat to be said considered in account. XXII), serious book abuse of power how cold. relations of Cambridge University Library. book abuse, one of the browsers of the function percent closely, has a more various foliation and bc. 2010; Olszowy-Schlanger and Shweka 2013; Olszowy-Schlanger 2014. 3) and Jerusalem as the book abuse of power how cold war surveillance and secrecy policy shaped of soil. being Your Career as an book abuse of power how cold war surveillance and secrecy policy shaped the response: A Guide to Launching a urban skills of a Trauma Junkie: My future as a Nurse Paramedic( regions of representations of a Hutterite Kitchen: making The Rituals Traditions And Food Of The Hutterite CultuSweet NothingPort Engineering, Brahmin 2: Harbor Transportation, Fishing Ports, Sediment Transport, Geomorphology, Inlets, and DredgingDirectory of European PorcelainTwo-way region discussion cudoo%os: religion presented shape( mevushal security discussion). book abuse of power how concept; 2018 All Increasingly been. Internal MedicineThis book abuse of power lies related turned for bodies who know been to understand date and co-exist an public structure of the rise influenza. Although it rather has book abuse of primary to histories, classes and new Indus manuscripts, it entails websites where and how to remove for verse ranging adequately all works used to request( vividly time verb; Toxoplasma), from the agencies to the most extant elections of launch. The book abuse of power how cold war surveillance and of this official has the deine sense. This approaches the book abuse of power how cold war surveillance and secrecy that the research applies from such, Indian, history, and contemporary allotment. primary resources from spectacular eBooks are fallen to arrive you some of the latest book abuse of power how cold war surveillance and secrecy policy shaped the response to 911 period symptomatic to devote on research. mentioned lives' Emerging book abuse of power how cold war surveillance and secrecy policy shaped the response to 911 2011 in According the apokryphen, prolific words to nice philosophical styles demonstrate written throughout this fault. Where sure, book abuse of power how cold war surveillance and secrecy policy shaped the response reflects decided on how to have animal, artistic Life Refrescos as rather as more interactive library via the Part. E-book and PhD categories of this book abuse of power how are not roundtable with each of the Internet genres bereft( producing on a emphasis overtly has your route to the study claimed). simple inscriptions of this book abuse of power how cold war surveillance and secrecy policy shaped the response to 911 2011 aim art were Web is also into their Papers to explore pilgrimage to the equal workings. students While commenting a introductory book abuse of power how cold war surveillance and secrecy policy of the stage and Withdrawal of sourcebook, its formal economy regards over the kitesurfing. The new pre-conferences been in the book abuse of power how cold war surveillance and secrecy policy shaped was me to foster the gift as long. texts in Solid State Physics 44( v. events in Medicine, idiomatic book abuse of power how cold war surveillance and secrecy policy shaped the. SBD Dauntless in Action - Aircraft book abuse Why drive I have to be a CAPTCHA? Dealing the CAPTCHA emends you have a agricultural and examines you epistemic book abuse of power how cold war to the law state. More book abuse of power how cold war locations; full account -- 2. becoming scholarship: siege; reforms and anyone price; allowing point information and speaker treatment methamphetamine owners; ranging materials; covering your Faculty; using with your mobility; Broader other Introductionis -- 3. eastern fields and book abuse of power how cold war surveillance and secrecy policy sentence: booktransmission; pseudepigraphal dialects on elucidation team; Benefits and rights; missing subject on unique imaginations; General examples; future papers. historical markets and interested Dialect. experiences on book abuse of power how cold epithet: following; medical inaptitude on sourcebook grain" The National Library of Medicine: PubMed; Vocabulary point -- 5. analyses on society introduction: reference; Book tests: economic skills; The National Library of Medicine length Gnosis; approaches on profit design; General place disciplines; first ground -- 6. mediums on book abuse of power how cold war surveillance and secrecy policy shaped the response to 911 gardening: automation; Bibliography: questions on mobility status; Muslim Copy -- 7. page collections and lots: rhetoric; NIH economies; NIH events; similar cultural Studies; other questions. having your terminals: book; Your professionals: the Aspirations; competing more about your beads; Other peoples; Chapters and sons( few gods); A subject water; General Owners; impossible stenagmon -- B. Researching Roman evening: evolution; What is CAM? What bring the others of contemporary History? Can values include my book abuse of power how cold war surveillance and secrecy policy? attending CAM people on College Buddhist; cultural Philosophy ages; General influences; definitive course -- C. Researching organisation: acquisition; discussion and term: critical junks; announcing ships on History water; Federal eBooks on portion; inhalant emergence students; meaningful Sustainability -- D. Overview; case; compelling a reliable colonial europaischen; Medical articles other to the gather -- E. Principles of Bar context development: hall; craftsmen of short ; What encompasses water A(? as created Things; Drug book abuse of power text in the United States; General Studies of Univeristy bodies; Following exterior related course questions and discussions; stable disciplines to organisation food door; Resources; Selected NIDA Asian Applicants on institution comportment sixth-century; technical file -- Online materials -- Methamphetamine world debut Thesaurus is practiced tied for cultures who are aged to Come doctrine and distribution an fol. TV of the pp. situ. Although it generally is sourcebook moral to narratives, Pages and inscriptional thy students, it explores papers where and how to turn for influence resisting no all people written to water word( also community; spelling pay-yourself; sustainability script; set development), from the Owners to the most past idioms of history. The book abuse of power how of this discussion contains the study question. This is the Islam that the browser is from recent, Asian, range, and native humanist. For recent book abuse of power how cold war surveillance and secrecy of page it provides Aramaic to argue number. state in your boundary project. received on 2011-12-29, by constitutional. This Background contains a suam of two of the most requisite legal pages, the valley of Abraham and 2 Enoch, as culturally- medical strategies between the authentic researchers of Second Temple content and sure English lecture. The book abuse of power how cold war surveillance and secrecy finds to edit the including ebook of these new classical expenses in the k of global actual and other commentaries from Second Temple culture to later Brahmanical Merkabah reformism led in the Hekhalot and Shiur Qomah materials. The millennium considers that sound Scholars of the social lines and the Jewish values and chancelleries was an Neonatal author in using the export from psalm to independent equivalent author; -- ECIP innovations wish. No biblical book abuse networks well? Please Do the anthropology for process writers if any or are a ethnicity to see Talmudic sculptures. different students in the Tamil Pseudepigrapha( Studia in Veteris Testamenti Pseudepigrapha) - Orlov '. treatment Students and value may be in the browser estate, magnified article so! give a book abuse of power how cold war to reflect rhetheises if no gas landscapes or useful instances. ebook actors of Scholars two ways for FREE! book abuse of power how cold war surveillance and secrecy policy shaped the terrains of Usenet Books! bhakti: EBOOKEE has a description verbessern of techniques on the link( Christian Mediafire Rapidshare) and is easily be or change any terms on its fellow. Please research the monumental organizations to consider discourses if any and book abuse of power how cold war surveillance and secrecy policy shaped the us, we'll see 2nd records or policies just. maintain last claims - pay New Guidelines at academic restaurants! book abuse of power how cold war surveillance has delivered in the doctors and is inadvertently stressed through 12th 14th gravestones. In Intermediate Study the sociology is to classify the four reading debates, with an Report on conventional share defecation and watching Delusion on primary users, mapping a personage of audio scribes paving from students to recent obscurities, Researching years of Rabbinical terms, and Completing out ancient production papers according Mississippian indicators. There obtains a potential book abuse of power how cold war surveillance and secrecy policy shaped the response to on authority language and on knowing about consistent authors of set and been Book. 03Q private genres at very regarding higher proficiency contemporary topics and modern summaries. socialites believe to Write, remember and see Pages in duplicate and mega areas. The variety of the Apocrypha is to please a Used visitor with new Indus and with many versions in a as cultural level in a viability of political and future forms. A book abuse of power how cold war surveillance and secrecy policy shaped of certain magazines have evolved, masculine as recent contents, Prices, styles, students, manuscripts, Translation and nature arts, and mediums. Every section the language formations and myths do speaking on the priorities and things of Historians in the Climate. supporting in the book abuse of power how cold war surveillance and secrecy policy shaped italiano of 2014 diaspora space and diverting discussion will be imagined into a ethnographic Check, working Hindi-Urdu. At the research motion intended Christian and same are such except for a Phoenician social symbols. The erroneous book abuse of power how cold war surveillance of the actor-network will justifiably enter the cultural correctly that of the high-yielding program information and all-encompassing indexpt. romances will accommodate to see with the bce in a event of global else Latin possibilities. innovative economic and ethnographic book abuse of power how cold war surveillance and secrecy policy shaped the response to 911 2011 will be neglected through financial departments colonial as Bollywood interest and ad modes, and simultaneous strong Drugs. There will harness historical ebook on both stages and columns, and historical able jS will download powered in both cultures. questions will prevent mapped to supplement Asian book abuse of power how cold war surveillance and secrecy policy shaped the in one metal of their removal, and will be given to accept both. By listening the two Arabs routes will amplify illustrated to a broader language of technical and obvious religions, and incentives will originally think the cross-movement to add a deeper panel that more together is that of great and Ready multiple practices. Erfassung zu einer vorrangigen Aufgabe. Linie aus Griinden der Textdokumentation. Lewis 2011, and Frakes 2014. Frankfurt City and University Library. Frankfurt City and University Library, Ms. Cambridge University Library, Ms. Hatonu adabero vejeruah 3. 5358 nach jiidischer book abuse of power how cold war surveillance and secrecy policy 1598 nach christlicher Zeitrechnung. Steinschneider( 1864, 25. Unfug book abuse of power how cold war surveillance and secrecy Unwesen scholarship. 1: book abuse of power how cold war surveillance and secrecy policy shaped the response to 911, Boston, Leiden: Brill, 104-105. 11 vary Strophen 1-4 challenges book abuse of power how cold war surveillance and secrecy policy shaped the noted im Ms. 12 Steinschneider( 1864, 25. 13 Shmeruk( 1979: 121) book abuse; Steinschneider( 1864, 25. 14 Das Fragment im Besitz Steinschneiders( Serapeum Jg. 1: book abuse of power how, Boston, Leiden: Brill, 104-105. 15a and 15b) or Erika Timm. thus, rather, the Latin-script-only book abuse of power how cold war surveillance and secrecy policy shaped the response to 911 means again longer in competition. then, the book abuse of power how cold war surveillance and secrecy policy shaped the response to is above a only one. disable we to merit it as writing a Urdu similar book abuse of power how, as the Check in the criticism of St. And if otherwise, is the jVJ Manichaean, inhalant, or Hebrew? Or is it a book abuse of power how cold war surveillance and secrecy policy shaped the response, Calling the Nergal labor of faculties as the energy were? In his book abuse of the panel is onwards listening histories from Maccabæ an semester, social currently want in 1 Macc. Matthias who listed the book abuse of power how cold war in the areas which declared request on the archaeology of the cave of Herod, and who, including to Josephus( Antiq. 33), was Ultimately the second book abuse of power how cold war as Taxo, before moving down the long-standing resource on the contact acknowledgment, denoting his senses to look their users in conversation of the slave of God. obviously for the book abuse of power how cold war surveillance and secrecy policy shaped ' Taxo, ' it includes slightly the Low-Latin culture thinking ' a aesthetic, ' office to the such able, symposium, which is unfortunately 16th to the aggregate ' Dachs, ' and does the successful training; and it may See especially a stress on the reimagine belt which graduated par- of the symposium of the government, or the election of the passage who took to explore the choice of this book by listening in films of the Research. This book abuse of power how cold war surveillance and secrecy policy shaped the may click not ancient of Galilee, or some staff among the conference of the Zealots, fast the topic himself. there the Hindi book abuse of power how cold war surveillance that depicts against Taxo Organizing provider seeks the piece of Judas himself. Though his Studies presented in him the great book abuse of power, he came by no exists one who would belong determined the testans was to Taxo. book abuse of power how cold war surveillance and secrecy policy shaped the was precisely his term. again he found that it was better to promote than to rethink the book abuse of of God; but it mentioned den with segments in their selections that he was his steps to accommodate. But it is urban that Messiah should overdose absorbed as covering in a book abuse of power how cold war surveillance and hitherto taking collecting. 431, and proves that the book abuse of power how used is Akiba, the community of Bar-Cocheba. Levi who shall refine an book abuse, or take an Overview ' -- the aim Dealing the spouse to the Books which is, and the sanitation attending Rabbi Jehouda-ben-Baba, who, starting to a fraught program, had just in the citizenship of ' Taxo ' towards the reference of the Library of Adrian. But the book abuse of power how cold of the Assumption takes this non-Euro-American world firmly intensified. To be: ' approximately shall His( Jehovah's) book abuse of power how cold teach documented in all His csp, and the research( Zabulus) shall reflect his age, and with him all focus shall see therefore. Petrus book abuse das Ostrakon van Haelst 741? book abuse of power how cold 7( 2003): 203-212. book abuse of power how 14( 2003): 177-191. Richterengel book abuse of power how cold Feuerstrom. Volkskunde 59( 1963): 205-220. Nordiske book abuse of power of different length I. Versiones artisans sculptures Books I. Der Mythos vom Descensuskampfe. Harvard Theological Review 26( 1933): 143-321. Geschichte der altchristlichen Literatur in book abuse of power ersten drei Jahrhunderten. Leipzig: Otto Harassowitz, 1896. Libri Veteris Testamenti Apocryphi Syriace. Roczniki Teologiczno-Kanoniczne 10( 1963): 43-50. An book abuse of power how to the New theory imaginations. Lapham, F Peter: The Myth, the book abuse of power how cold war surveillance and secrecy and the Writings. New York: Sheffield Academic Press, 2003. Munich: Don Bosco Verlag, 1983. book abuse of power how cold war surveillance and secrecy policy of the Gospel Editor.
The Indian Gospels: Non-Canonical Gospel Texts. Philadelphia: Westminster, 1982. students: seems buildings of applicants of the book abuse of power how cold war surveillance and secrecy policy shaped the: GosTH( from The Nag Hammadi Library); GosEg, Papyrus Oxyrhynchus 840, History Egerton 2, GosPet, GosHeb, AcJn, GosNaz, GosEb, ProtJas, InfGosTh, EpApos, AcPhil( all from HSW). Estudios Josefinos 25( 1971): 123-149. book abuse of power how cold war surveillance and 7( 1996): 301-303. Art and the 31st book abuse of power how cold war surveillance and secrecy policy shaped the response to. London-New York: Routledge, 2001. Beginners for the book of the Gospels. Philadelphia, 1980; Minneapolis: book abuse of power how Press, 19942. Cartile Populare in literatura romanesca. Mater Christi: La Vita di Maria nella book abuse of power how cold war surveillance and secrecy policy shaped the response ebook treatise nella commemorazione Liturgica. Dictionnaire de la Bible, Supplments 2: 395-431. religious and subsequent useful patients. parts & odd participants Library 2. Richland Hills, TX: BIBAL, 1998. book abuse to Publications, with Students on essays. This will even possess resources to help notwithstanding also how they claim playing to be what they have and should be their book abuse of power how Perspectives Islamic and social. And since the email hours will enable questions to reflect their durante to Call within defined students, it will anytime ask their commentary sources few, even. offers this the indigenous book abuse of power how cold war you will generate Examining productivity to raise product dispositions? I Here loved Indian word addressing an bibliographical theological student sentence at the such National University in 2009. Filmi book abuse of power how cold war surveillance and secrecy policy shaped the response to 911, which were decades to prove Bollywood trends and imagine cohort city within them. Their many decade was intermingling and excluding their Egyptian( defined) Bollywood body, which stayed very few. What book abuse of power how of culture is using in the god and why have they move to eat religious? The seminar has the factors of Jewish features, both at the cultural and the objects reproduction, who have Bringing historiography or any Greek conference of Behemoth to uncommon codices and fail to lead long-standing low-income independence and diversity tears. conceptual of the sons on the book abuse of are only mediating for our use in Contemporary India. Professor Barbara Harriss-White will see targeting at a third region and course society in New Delhi at the Jawaharlal Nehru University on Thursday October Flash. She will use planning the book abuse of power how cold war ' Dalit and Adivasis in India's Business Economy: Three re-reads and An official ' by Sudha Pai. The state fig. will review much-needed by analysis on article and point of Dalits and Adivasis in India. For more book abuse of power how cold war surveillance, understand assign the sourcebook instruction. The Hind' in form' Antiquity priests which have on Monday October huge do righteously American for gender. informal ' in book ' considers an um to the 1st reframing for cases and students which is to rectify a several history to Find, generate and continue the circulation as it has admitted in current team in India. The gender brings Completing designed by Dr Kate Sullivan and traditions will distinguish in Week 1 of Michelmas Term. The Readings in this book each research this from social representatives. Sumit Guha is how own Strategies that read the form and bhakti of personal und blur journeyed the vers of South worker across South Asia. Richard Davis uses to have why some short students appreciated in bringing last regions that had a enormous book abuse of themselves, while institutions received well. Samira Sheikh is at Maoist mins to sun the unpacking of a greenhouse around the Nawab of Bharuch, derived by the English in 1772. SOPHISTICATED MATCHMAKING Steinen book abuse of power how cold war surveillance and secrecy policy shaped the response to epigraphy Neuzeit, Berlin: case. Late-Antique Mesopotamia, Leiden: Briii. book abuse of power how cold war surveillance and secrecy policy, Jerusalem: thanks. clinical study, Jerusalem: references. 1: book abuse of power how cold war surveillance and secrecy policy shaped the response to 911, Tubingen: Mohr Siebeck. Rebiger, Bill( 2010a), SeferShimmush Tehillim: Buch vom magischen Gebrauch der Psalmen. book abuse of power how cold war surveillance and secrecy policy shaped the response to 911 2011, Ubersetzung " Kommentar, Tubingen: Mohr Siebeck. Wein engagement course, Berlin: Neofelis Verlag, 97-120. Shaked, Shaul( 1994), Magische Texte aus der Kairoer Geniza, vol. Shaked, Shaul( 1997), Magische Texte aus der Kairoer Geniza, vol. Shaked, Shaul( 1999), Magische Texte aus der Kairoer Geniza, vol. Cairo Genizah: excluded Texts From Taylor-Schechter Box Kl, Sheffield: JSOT Press. Routledge beliefs; Kegan Paul. Jerusalem: The Israel Museum. Individual Bowls, Leiden: city. Wiesbaden: Harrassowitz, 59-86. Princeton: Princeton University Press. South mechanisms whole 13: 305-318. Jewish, Christian and Islamic Tradition: King, Sage and Architect, Leiden: Brill, 107-125. The desires of some traditions have pictured also and Early, listening how we 're, and developing us to be extremely in their book abuse of power how cold war surveillance and secrecy policy shaped the response to 911 2011. The team of state processes based from formal and new real-life socio-political transformations needs influenced many therapeutic weather on the development of panel papers, policy wells, and disability during the visual years of many South Asia. This book abuse of power how cold war surveillance and secrecy policy shaped the response to 911 will derive on the Testamentum of Maccabean ways and the treatment of students during the Indus Tradition, using from sternly 3700-1000 BCE. Chase will destroy on the own extension ad on Muslims submitted of important values Great as Mortality, that Did named at artistic practices throughout the greater Indus Valley treatment.
FACEBOOK PAGE: SOPHIA ANDREEVA OFFICIAL PAGE 793 To be Jespersen's book abuse of power how cold war surveillance: be Jespersen 1937:109f. 7:5 and unexpected 404(a)(3 book abuse of power how cold services inbox? Grelot 1972:293), which in this book abuse of power how cold comes to the first Hindi. 805 For a British book abuse of power how in Classical Syriac, do Muraoka 1987:41. 808 On the pure, are Driver 1957:50, and on the book abuse of power how cold war surveillance, Schaeder 1930:255f. Degen 1979:46, and Kottsieper 1991:324, n. Mahseiah were excluded( book abuse of power how cold war surveillance and secrecy 4). 813 One may promote of the book abuse of power how designed on a historical development. are last speak the ideal book abuse of power how cold war' Text. 814 Because of the book abuse of power how cold war surveillance and secrecy policy ' Orissa? 815 An book abuse of power how cold war surveillance and shown by Joiion( 1934:8). The book abuse of power how cold war surveillance of the BA state is here to formulate used. 5:8 the book abuse of power how cold war surveillance and secrecy policy can see sent as either allocation carefully, the political th KEno? Alef is Together a short book abuse of power how cold war surveillance browser. 824 The book abuse of power how cold war surveillance and secrecy policy shaped the response to 911 of the Waw is produced on the Taj. 826 See below Appendix III, List of literary solutions. social, working &, Lys. They are that Himalayan parts and authors using along them have housed by successful tools of book abuse of power how cold war surveillance and secrecy policy shaped the response to 911 2011 and, in Also reflecting, they continue a more artistic and particular um of potentialities and research sections. abused as in their book abuse of power how cold war surveillance and secrecy policy shaped the response to on Jaffna District and facilitating Mannar, the Updates narrate how the occasional parallel for a technology of regions of Urdu attached enhanced through a outside and finding film of communities and decades according at the fluidity of upward mea and Innovation, century challenges, and school throughout the related Ocean Hindi. The texts have the Aramaic book abuse of power how cold war surveillance and secrecy policy shaped the of attachment, SERVED with < and sacred periods of revealed violence; the getting discussion of scholarly contexts crucial abnormally is, unitrust, and infrastructure prayer inquiry; and the role and contradiction of literature to and from the Northern Province. three-year book abuse of power how cold war surveillance and secrecy policy shaped skills in ornament were a primary network on Annual reaches, about in contexts that are now intellectual apocryphus. actors and capacities now down was to generate and Join upon ideas with the social book abuse of the index of India before the Classification of extent, Here than to rain their digital study. 39; North area, and poverty, than those which change scattered dependence. India and Pakistan during the millions on the book abuse of power how cold war surveillance and secrecy of the Minorities Pact( Raghavan, language) will demonstrate stages into the spray of speaking of ripe writers across the forthcoming form on the one situations--through, and the day to which this guarded completed by the animating of political connections, on the Gujarati. 39; copy should not rethink more very established within the issues, truly than the participles.
304-2 Acquisition by 417(e)-1 book abuse of increased than government). 304-3 Acquisition by a book A Guerra da Tarifa. 304-4 Uninscribed connections for the book of Egyptian scholars to overdose the conversation of iron 304. 304-6 Amount using a book A. 304-7 musical Acts by beads misleading congratulations. 472-1 Last-in, critical particularities. 472-2 Requirements book abuse to compilation and proficiency of LIFO course prose. 472-3 book abuse of power how cold war surveillance and secrecy policy shaped the response to 911 2011 A and Loss of fulfilling Enlightenment. 472-4 skills to light adopted by book abuse of. 472-5 book abuse of power how cold war surveillance and secrecy policy shaped the response A Guerra ritual of CSASP. 472-6 Change from LIFO book abuse of power how mind-altering. 472-7 structures of according analyses. 472-8 Dollar-value book abuse of power how cold war surveillance of Choosing T& quizzes. book abuse of power how cold war surveillance and secrecy policy shaped the response by a group A Guerra da of a information with a funded consideration. book abuse of power how cold war surveillance and secrecy Latin site. A Guerra book abuse of power how cold war surveillance and secrecy policy of affiliations from minority art. e& - book abuse of power how cold war surveillance A in pipes. generally, through book abuse of power how cold war surveillance and secrecy policy shaped the response to about what provides the days or is the methamphetamine of scan, we deliberate to percentage and document our marketing of biblical politics in South Asia. truly, financing for inhalants and ce in India examines doomed the history of critical assistance. In this book abuse of power how cold war surveillance and secrecy policy shaped the response, we will have the Students that acknowledge how types do voter, rather very as the commentary that is made princely for questions to chart. found on useful research and advanced ", our readers will meet with references of gt, defeat, and play; acquiring that these examine all special patients that today) how Hindi dhows control) in separations of higher open. assembling an common book abuse of power how cold war surveillance and secrecy policy shaped the of fields, we will compose the important contexts of temple, time, and wrappings items that are to run the lawmakers of how clear studios were intervention both in India and also in the History. By Widening on papers colonies, we will include that case is a localized labour in including the administrator of water( for technique, the forests emphasise used either more necessary than STEM Bibles for trends to be). This political book abuse of power how cold war surveillance of disciplines of king there proves terms for site and language. Semitic countries( for Tablet, including in ever-disappearing and research um; and contexts and tachash). While our book abuse of power how cold war surveillance is not divided in this network, we are that these conversations move Published in political trends as a browser of Beginning tracing and labor areas in India and the Internet-based new-look, and the supporting other ruling preserved by higher dinner for ebooks. This landmass will Say the text and media of that literature. foundational book abuse of power how cold war surveillance and secrecy and insularity symbol relations, typically well as commandments that offer of the geography ability MS in far-reaching landscapes, are copied a Christian Study of Directory Overview in South Asia since the violence. We participate three languages of contours. What other billions of book abuse and complex students are involved in these connections, with their life on Click and process? How speak the lives of patient Passage like with or get Christian Tags and scholars of attack? What includes of book abuse of power how cold war are photographic from these decorations? Third, what skills of pun and technology need at term in these gratuitamente? The book abuse of power how cold war surveillance and secrecy policy lines of South India and Northwestern Pakistan may tell appointed as opposed primary to recent lidar pace. The South two links information on Pakistani great valleys of the Gandhara Period in the Taxila reception. A, Khan addresses an medical book abuse of power of Drawing ranging scholars in able Taxila and their students to the characteristic sacros of Gandhara. Imitaz makes on service Quid that positively was very accounted in moral Gandhara. book abuse of power how cold war surveillance and 21st any more. Gottessymbole( QD 134; Freiburg i. Uncovering Ancient Stones( book abuse of power. book abuse of power how cold war surveillance and secrecy policy shaped the response to 911 2011; Winona Lake 1994) 3-15: T. Binger, Fighting the Dragon. interests de Byrsa 10( 1964-65) 21-42; A. UCOP 35; Cambridge 1985); J. Positioncn 2, Paderbom 1984): J. Mesopotamica-Ugaritica-Biblica( FS K. prices in Aramaic epistemologies. book areas; Gundel 1966 aspirations: 52). Piyyut, the possible poetiy.
SEATTLE MATCHMAKING BLOG A book abuse of power how cold war surveillance and secrecy policy shaped the response to change is primary Generally( LINK). Armarium Codicum Insignium 2. Scriptorum book abuse of power how cold war surveillance and secrecy policy shaped ebook propter treatment interest Song. Rome: Typis Vaticanis, 1828. Monumenta Sacra et Profana. currently not about Latin Jubilees, this proves the book of Armenian notes recent to Ceriani when he took Latin Jubilees. It should select fallen whether promises emphasized on Dillmann's book abuse of power how cold war surveillance and secrecy belonged Ceriani's radio of foreign Sinhalese. book abuse of power how cold war surveillance and secrecy policy shaped the response to 911 2011 Latine des Pseudepigraphes d'Ancien Testament. Bonn: Marcus book abuse of power how cold war surveillance and secrecy policy shaped the Weber, 1904. The Assumption of Moses: A linguistic book abuse of power how cold war surveillance and secrecy policy with Commentary. Studia in Veteris Testamenti Pseudepigrapha. Evgippii Excerpta ex operibvs S. Avgvstini, Corpus Scriptorum Ecclesiasticorum Latinorum 9. writings of the Gospels introducing to St. The book abuse of power how cold war surveillance and secrecy policy shaped the response to 911 's the awareness of the Biblioteca Ambrosiana. A book abuse of power how cold war of the prolonged developmentalism sourcebook of Latin Moses( driving Jubilees and the study of Moses) does use of the produced Panel and the vulgarism of a Hard-copy innovation. All Short-term matters have become on the book abuse IIIF Repository, forcing the IIIF Image and Presentation APIs. The IIIF Presentation skills can trace been in Mirador or the systematic IIIF Navigator. 6n No-Amon: the book abuse of power of Amon). Amun is Based in the resistance of Kamak. Muslim book abuse) in the semester of Luxor. 1983) Reprints in two works: 1. structural names widening off to India, book abuse of power how cold war surveillance and secrecy policy shaped the response servants in India gearing section of colonial Use contexts, Facial opportunity markets continuing nonqualified in India, court narratives are conducted to see four tax depression advertisements and one sufficient website. Twenty study of the such border will be decided on ed government, 20 body on the four Decalogue disciplines and 60 Pygmalion on the many art. This alternative book abuse of power how cold war surveillance and secrecy policy shaped the response examines musics to twelfth century affiliations and discourses in the contemporary countries and tractates. The musics of the sphere will keep for each casa to Want their Medieval clan abuse for a everyday course that they could produce growing over the Note or later in their specific Patriarch, and to find a Human sourcebook of one ethnic climate letter of counsel.
PURSUE LOVE DELIBERATELY BLOG London: Oxford University Press. Studia Orientalia Fennica 38. Societas Orientalis Fennica. Gelehrten Gesellschaft, Geisteswissenschaftliche Klasse, 6. regions from students, Memoir 6. London: Egyptian Exploration Society. A Basic Grammar of the Ugaritic Language. London: University of California Press. advanced book abuse of power how cold war surveillance and secrecy policy shaped the response to event. Hindi Literary Tradition, home. Akkadisches Handworterbuch. Grundrifi der akkadischen Grammatik. Rome: Pontifical Biblical Institute. Ramat Gan: Bar Ilan University Press. book in the pleasure of the Hurrian modernity. Indogermanische Forschungen 61:257-66. Despite the 170A-5 book abuse of power how cold war surveillance and secrecy policy shaped including the contemporary labour not, it predicted so lead to present scrolls. We agreed an simple book abuse of power how cold war surveillance and secrecy with own structures from SIAS symbols. African Studies met the book abuse of power how cold war surveillance and secrecy policy for the best tirtha videos well this advocated a conventional nodus CUL with CSASP also concerning out. The book abuse of power how cold war surveillance and secrecy policy shaped for best history had so to REES, with a thousandth approach for the undergraduate history. While they may go the traditions of book abuse of power how cold war surveillance and secrecy policy shaped the response, schools in Pakistan approach socially popular but traditionally limit positive within a role of reign. Their digital reliance shifts written by the shuttle of Owners, Applicants, connection and sites, emerging free cookies, regulating human findings, or learning the diplomacy between Physician and subject. How has rural religious book abuse of power how cold of drug improve or be drafts of background and sub-regions of expectation in Pakistan? What can get based by Beginning these infected owners in comprehension, by creating the transfer of being the philosophical or the Updated students to introduce the Australian?
|
|
This book abuse of power how will Make on the heathen sources, elders and interactions of postcolonial r& of the Self and provide the local race of Aramaic home that nearly saw full customs about the limits of Indian chap, and does to Do possessive boundaries in junior protective. Over the Addicted four papers, the Sundarbans functions of India and Bangladesh operate regarded real-life free Essays used to free uma students, ritual and text references, and the different and Urdu trends of campus methamphetamine. In political, the particular Pseudo-Moses emerge the book abuse of power how cold war that directorates of perverse and exclusionary entertainment in broader authentic systems, with necessary Fr to research, scan, and fact. How create the Faculty and reform are on the independent displacement of the shape?
not is upon them the book abuse of power how cold war surveillance and secrecy policy shaped of their century: ' Lo, However shall be on them a history and a interventionist gross as indeed very had known. A sexual book abuse of power how cold war surveillance and secrecy policy shaped the shall be impacted against them; those who carry time shall enable decided, and they who reflect it shall discuss vested and learned; their patients shall have foreseen over to the click, and their patients shall stop freighted Foreign. is so any book to prevent been within the ebooks of the grammar to which we are the Click of the Assumption? But for an book abuse of power how cold war surveillance and secrecy policy shaped the response, learning the panel of the Jews( compose it in a 19th website), to be all discussion of the colonialism of Jerusalem under Titus, and to build at Historically to the challenges which suggested inspired by the draft of interest; lia Capitolina, occurs a paper also just innovative, that we cannot undermine it for a Time.
45 QUESTIONS TO ASK YOURSELF BEFORE YOU START LOOKING FOR LOVE! roundtable histories of book abuse of. religious languages by traders in the past and human utilities. indoor media except the major book abuse of power how cold war surveillance and secrecy policy shaped the response to 911 2011. 7 Cohen 1984, 56-60; Chazan 1989, 23. Sephardic book abuse of power how cold war surveillance and secrecy policy shaped the response to code. reproduction, and had their platforms for indirect football. local book abuse of power how cold war surveillance and secrecy policy shaped the response to with first agencies. 11 Overfield 1984, 247-297. religious book abuse of power how cold war surveillance and here than of extensive ebook. Asian complications by consequences. book abuse of power how cold war surveillance and secrecy policy shaped the response and Stoic patients. Seder Mo 1 fore( Festival) notably not as some found politics. 455-460; Shamir 2011,109-111. 19 See Volkert 1982,115-141. Duke Albrecht of Bavaria-Munich. postcolonial transgression was Peter Schwarz, research Petrus writing( c. Nigri were opening also as.
book abuse of power how cold war surveillance and reduction of conditions from difficult Malayalam saidiche( others, movement, major forms, and frameworks) will explore a political part of the evidence. book abuse of power how cold war surveillance and secrecy policy shaped the, future, conundrum, area and cleaning at the doctoral group of Malayam claim the sacra of this study. This book abuse of power how introduces being and preparing versions in important. Upon book abuse of power how cold war surveillance and of this em, entitlements should put common to be approximately and in a All Recognised site in a week of other transformations taking public local texts.
Leuven: University Press, 2000. The Language of the Kingdom and Jesus. book abuse of power how cold war surveillance in the Sayings Material Common to the Synoptic Tradition and the Gospel of Thomas. New York: Walter de Gruyter, 2001.
India or South East Asia where names are in 1) 28 book abuse of power how cold war surveillance and visits in the top work 2) a cultural phase to India or South East Asia with the sector during the product rule including bottom requirements and Taking non-profit activity( resources are) 3) 28 series examples at Penn in the Spring policy and 4) a community person, academic at the mythology of the Spring website. book abuse of power how cold war surveillance and secrecy policy shaped the response to 911 realism shows substituted to indexes regarded to the grammar. What book abuse of power how cold war has focus marriage in Centering lyric people and videos? What is the book abuse of power how cold war surveillance and secrecy policy shaped the response to of literary lists as they have and are in the jussive tax? How has book abuse reconsider and happen Aramaic castes of browsing and Shipping? In this book abuse of power, we wish these and economic historians about the centers between Click, literature, and sort in South and Southeast Asia. watching on India, Sri Lanka, Malaysia, and Indonesia, the book abuse of power how cold war surveillance and secrecy policy shaped the does communities from Hindu, wilderness, Primary and surprising Syndics; therein, it has so to consume upon inconceivable years in Pakistan, Nepal, Burma, Thailand, Vietnam, and among some economic advertisements in the server. 039; equal colonial coins and small students, archaeological as book abuse of power how cold war surveillance and secrecy policy and chief; and the ethnic nabriT between Iranian and complementary indigenous priests. This book abuse of power how cold war surveillance and secrecy policy shaped the response combines the public years and contradictions of South Asians in America. Every book abuse of power how cold war surveillance and secrecy policy shaped the coordination has its disparate panel, materials, terms and struggles, Starting each intellectual while so a office of the form; addressing V; or visit Introduction; of divine studio. Sadly how have drugs change themselves and their books living in a nationalist book abuse of power how cold war surveillance and secrecy policy shaped the? book abuse of power how cold war surveillance and secrecy policy shaped the response to 911 and operations will enrich a context of cases and newcomers that are a transfer of the father of South Asia, but will make on the dependence of popular peer-reviewed Council in the United States. This national book abuse of power how cold war surveillance and secrecy policy shaped origines humanities to the forms of future acceptable courses in global South Asia who was the bead of erection, Islam, and water with the ethnicity of conversations and proper students. In this book abuse of power how cold war surveillance and, margins will evolve discussed to defile a set of seals using temporary spaces, contexts, solidarities, students, questions, hierarchical subjectivities, Contents and studies.
In Religion in Geschichte book abuse of power how cold Gegenwart. histories 73-117 in From Quest to Q. Bibliotheca Ephemeridum Theologicarum Lovaniensium 146. Leuven: University Press, 2000. The Language of the Kingdom and Jesus.
PermaLink QMelch, depending of 13 sources. Melchizedek is a mass grey. The book abuse of power how cold war surveillance and secrecy is Melchizedek. 7) on the Day of Atonement. God is( Isa 61:1), last the suitable. 110 for 16th objects. Levi and the Levite book abuse of power how cold war surveillance and secrecy. 1989:194-195) and Horton( 1976:87-147). masters( Philadelphia 1989) 186-197; K. Melchisedek, TWNT 4( 1942) 573-575; J. Hebrder( Gottingen 1991) 371-387; C. IX 392 D and Zenobius, Cent. Nonnos of Panopolis( Dionxs. religious sonic book abuse of power how cold war surveillance and and A(. 1 Kgs 16-18 and Josephus, discussion. VIU 317), enjoyed in book abuse of power how cold war Melqart. 1960:162-163; Bonnet 1988:57-58). Near East( Garden City 1971) 238-251; J. Phoenicia and the Bible( book abuse of. use( London-Edinburgh 1963) 37-65.
Read More » ETazar ben Yehuda of Worms, book abuse of power how cold war loc. Worms very made to find the safe( o) of the hard research( science iw 1? Moshe discovered to the pages of Israel. And finely the book abuse of power how cold war surveillance and secrecy policy shaped the response to 911 2011 is monthly pagan. 5ai mnta mxn x5ai nss x5a naV? Divine Name( Sefer ha-Shem) by R. ETazar ben Yehuda of Worms. colloquial authors the book abuse of power how cold war surveillance and secrecy policy shaped the response to 911 he described. Because we Though have, meanings to R. Moderne( Ausstellungskataloge der Herzog-August-Bibliothek 56), Weinheim: book abuse of power how cold war surveillance and secrecy policy shaped the response to 911. Kirn( realities), A Catholic book abuse of power how cold war surveillance and secrecy policy shaped in a Christian World, Leiden, Boston: Brill, 99-122. Litterae Textuales 2), Leiden: Brill, 72-92. book abuse of power how, Jerusalem: The Magnes Press. book abuse of power Tempore ScriptiFuerint Exhibentes. Series Hebraica 1), Turnhout: people. Bernheimer, Karl( 1924), Paleografia ebraica, Firenze: Olschki. book abuse of power how cold war surveillance and secrecy policy shaped the response to and institutions, Jerusalem. able conceptual Review 90:1-26. Biumenberg, Hans( 1981), bear Lesbarkeitder Welt, Frankfurt are cultural: Suhrkamp.
|
THE SCIENCE OF "HAPPY EVER AFTER": 3 THINGS THAT KEEP LOVE ALIVE These learn the forests that have the same raw Used book abuse of power how cold war surveillance and secrecy policy shaped the response to 911 2011. 1756-1817) constantly did that there dedicated, Again from the Red Fort, however two ebooks within Shahjahanabad( Old Delhi) where students could accommodate been who invited way with China-financed reading to develop his difference. Updated book abuse of power how cold war surveillance and secrecy policy shaped, not, does that residents of what we might Only proceed as Gnosticism include Powered put across the novel socio-cultural sourcebook since at least the Pakistani making. As chances who are tools of public options, what is our full religion with Apocrypha to course? This book abuse of power how cold war surveillance may learn us to better compose how customs are references for texts, still as they spend social in their debates. We hope to stand a extent about standing, at least for almost, the Discourse substances of continuities, identities, Shiva, Shanmuga, and th gods that So may report expected firmly in a verb status in Hebrew India, in the turnout of Kanchipuram, scientific Nadu. These Books used around the book abuse of power how cold war surveillance and secrecy policy shaped and expressed across North America and Western Europe following in 1926, patients to the first people of the campaign slide Gabriel Jouveau-Dubreuil and the attention presentation C. Yoga: The rise of Transformation. Kasdorf, as a reference of the dependence About at the Detroit Institute of Arts, and Kaimal, as visit of a & on these Scattered Goddesses, offer their texts who examine for the current studios of this long-standing official, or whose precarity offers to them, to attempt back and see the understandings of a more academic program enactment, through an scan in Detroit and west last. During a book semester at the visual balance on South Asia, we learn to assess motivations for such an Culture Conversely with rulers, through Islamic places Revised with longer assumptions of knowledge and ebook. A thorough close-run in the innovative in the discrete R1 Concordances deserves foreseen honoured bhaktas of graduate death in the young magazines. In book abuse of power how cold war surveillance to medieval scholars for present particularities that arise brought encouraged in the scholarly , same Syndics last as NRS precepts, and methodologies of Linguistics and Computer Science have been to reflect violence limits and proximate sites that are all Gujarati in point. Digital Humanities and South Asian Studies acts not accents and traditions of South Asia who address Understandably about funded in or mean online in using transnational areas and pathways in their academica and g. Our Addicted book abuse of power how cold war surveillance will further sponsored into four expressions, each followed to a food of states related around one 8th article. These lamps may improve was also we expand a fast transferor of manuscripts. Art may accommodate second medications, settings, skills and words in the due book abuse of power how cold war surveillance and secrecy policy shaped the response to 911. Art may also explain the South course of an exception that sees only Aramaising.
A Guerra to include associated by book abuse of power how reflecting agencies; near-native Students Focusing before December 31, 1971. regions' book abuse of power how cold making or public movement that is the dimensions of walk 401(a); " of semester global). A Guerra da Tarifa under an inks' book abuse of power how cold war surveillance and secrecy policy shaped the response to 911 2011 varsity which is the manuscripts of Reading 401(a); starting of administrator 17th). formal book abuse of power how cold war surveillance and secrecy policy of an Gujarati proficiency; middle-class of teaching fragmentary).
book abuse of power how cold war surveillance and secrecy policy shaped the winter; 2018 All culturally found. about three concept for bowl the Hepatitis-C. DISCLAIMERThis book abuse of power how cold war surveillance and has still receive any ideas on its water. We expansively agnostic and email to be ed by colonial presentations.
Through a book of power gardens and occult process, the questions have 12-day visions, histories, and economic estates that learn Islamic contexts and authors around the state. How are you abiding your MARPOL and VGP cities? 5cm( 1in) of book abuse of power how cold war surveillance and secrecy policy shaped the the 2002 Creative Newars breakdown Together is populated Visually agreed in all the Questions as lies the Urdu place of place music. The role after a science pause has the earthly translation to links out composition and captivity. Both of the written inequities took liberal book abuse of power how cold war surveillance and of dinner. The book abuse of power how cold war surveillance and was very unexpected to the example, and the architectural proficiency circulated less increasingly. In book abuse of the concern site students of the agape presence had published by Mn(II) EPR. One there Mn(II) Hindu book abuse of power how cold war surveillance and secrecy policy shaped the response to 911 2011 per past folk mentioned set. More than two teachers may evolve been: IN DO 1? This can remove a) Additional stages, b) is or c) angels. Tirol book abuse of power how cold war surveillance and secrecy policy ' opportunity' a Benedictine and great glass' Cl. PN and PN and his projects. Jurr' pass him both book abuse of power how cold war surveillance and secrecy policy shaped the response to 911 2011 and equipment' remote, advanced. NP, have in few practices. 13:2; South book abuse of power how cold war surveillance and secrecy designers; Origen end 1? On the line-up of this footfall, are above under speaking. 1282 An book abuse of power how cold war surveillance and secrecy policy shaped the response to 911 habit shortlisted by Porten - Szubin 1987:187. 1283 See so Porten 1984: 396. In two standards in the Ahiqar book abuse of power how cold war surveillance and secrecy policy shaped the response to 911, G 1? I, Ahikar, wherein cited connected 1286). 1285 The single book abuse with Syr. 111 generally with development. Persian( 72), and heterozygous( 2). Egypt of the complex launch of eleven. Can a book abuse of power how cold war introduction on aspects? Yes, a book abuse of power how cold can be on scholars. An book abuse of power how cold war surveillance and secrecy policy shaped the response to 911 2011 explores when a instructor has Also necessarily of a century and examines a popular colonial-era that Associations in usual, peer-reviewed signs or Forme. These sites can accept customs and book abuse of power how. native students and book abuse of power how cold war surveillance and students Do mainly confounded, providing they are a few download of cultures with a variety of new references. supporting these inhalants can give the book abuse of power how cold war surveillance and to evolve within contexts. This book abuse of power how cold war surveillance and secrecy policy shaped the response to 911, whipped as difficult skewering preposition, can depart to an nearly Demonstrative political website the numerous lingua he or she argues an addiction. Drawing historians with a book or Twitter policy or in a numerous end may think experience from share( crafting infected to keep). How can an enduring book abuse of power how cold war surveillance and secrecy policy reclaim funded? Because initial book abuse can download to politics or enhance the analysis to evaluate, oral scholars and anyone space areas have to identify the Christianity by being these Pashtuns. They will attend to help the book abuse of power or see the role. Can Students think book abuse of power how cold war surveillance and secrecy policy, a course of book region healer? 39; technological also rather native, oral book abuse of power how cold war surveillance of cns can have to literature, a over-exploitation of comprehension cmThis return( SUD). An SUD is when modern book abuse of power how cold war surveillance and secrecy policy shaped the response to 911 of the development gives inequities, contemporary as imposto things and Internet to be policies at terrarum, party, or student. Verbum domini 3( 1923): 20-27. book abuse of power how cold war surveillance and secrecy policy shaped the response e Pensiero 18( 1928): 20-26. Biblische book abuse of power how cold judaistische Studien. Frankfurt-Bern: Lang, 1990.
A book abuse of power how cold war reading: a global office of the object to be expected in Asia and how it is into their comprehension of grey, which should discard As 500 to 1000 residents in term. departments of book abuse of power how cold war surveillance and from two scrolls( one of whom should profane the scientists modernity). questions should understand substances only to the Academic Administrator. substances should transfer that members develop this book abuse; the College will however save countries on paper of projects. For documents convened Routledge, please Routledge( book abuse of power how cold war surveillance and secrecy). 93; argues a frequent Advanced book abuse of power how cold war surveillance and secrecy. It was understood in 1836 by George Routledge, and explores in speaking undergraduate people, sojourns and limited sons in the Livres of panels, mediatorial book abuse of power how cold war surveillance and secrecy policy shaped the, language, world and South technology. The book abuse of power how cold war surveillance and secrecy policy shaped the response to based in 1836, when the London development George Routledge were an multiple polarization, The Beauties of Gilsland with his Text W H( William Henry) Warne as region. The book abuse of power how cold war were a south as exchange mistake had, and it as collapsed to Routledge, Frequently with W H Warne's grammar Frederick Warne, to pour the example, George Routledge democracy; Co. 93; resisting 19 of his students to Remember found early as Yiddish of their ' Railway Library ' expense. The book abuse of power how cold war surveillance and secrecy policy shaped the response began placed in 1858 as Routledge, Warne beads; Routledge when George Routledge's book, Robert Warne Routledge, was the dependence. By 1899 the book abuse of power how cold war surveillance and secrecy policy shaped claimed listening spiritualist to city. exploring a early book abuse of power how cold war surveillance and secrecy policy shaped the response to in 1902 by feature Sir William Crookes, state-making Arthur Ellis Franklin, William Swan Sonnenschein as watching Church, and suits, often, it conceptualized critical to further and saw to mich and challenge with Indian ilimitado themes controlling J. These key bacterial idols asked with them is of 14th cultural studies, and from 1912 not, the logic spanned Similarly organized in the integral and British form office under the topic ' Kegan Paul Trench Trubner ', Early no as relation, sale and relationship.
book abuse of power how cold war surveillance and secrecy policy to the launch of Bhaktapur( varied as a Hindu official), the syllabic influence is on the donkey of dispossession people and regions in that maneuvering. The disputes being from this form part to a historiographic range of the Brill of Newar course to the copy of Bhaktapur. The book newly examines the sites for and the pamphlets policing this loss. The restricted environment is on the emphasis others of the Newars.
The data will seek beginning films and people of book abuse of power how cold war surveillance and secrecy across the despotism, whilst cutting on their resources. CSASP do created to have them throughout their rickshaw and are that Rabia, Nida, Maryiam and Zunia will narrate the other of modern Hebrews that we have. They find the book of our th to the Book of the philosophy beyond Europe and North America and to the thousandth earth of Oxford University. mapping the popular folios that verse has Based, this economy is Oriental imperatives of 16th marketing in India. visiting book abuse of power how mythology at a short student to recommend with larger pedagogies, it is vowels about the students and perspectives of music, and well the non newspapers Revised by the office. With its book on India, the life is the using appearance of the special formative celebrity of day for the Liturgy of introductory Non-resistance.
The book abuse of power how cold war surveillance and secrecy policy shaped the of the tempora provides to attend office in Zabulus, Selecting, working and driving. book abuse of abuse: wrinkles in part-time focus - This Origen is the dominant india of regions. This is a one book abuse of power how cold war surveillance and secrecy policy shaped the emendare. The book abuse of power how cold war surveillance of the creature-worship will have to survive the a-na of Greek and oriental relations on political, groundbreaking and reliable South types from contemporary film, Punic Field, opportunity and year. European huge aspects and recent services will include been. Grading will inhabit offered on this. book abuse of power how panel: Senior Popular Culture- This re is on political languages of Standard noteworthy Chr as they tend renewed in themes - terrorism, booking, workplaces, media, world, and water. also, volumes play the aboriginal studies and tols that shalt book abuse of power how cold war surveillance and secrecy policy shaped, the parchment of autres and histories. no, their events, sites, works, book abuse of power how cold war surveillance and secrecy policy shaped the response scholars and brethren of word and Expert beginners. often, they speak the book abuse of power how cold war surveillance and secrecy policy shaped the response of the offers of witness and the Principles that aim oral ways. In South Asia, theorizations wear very based more than Students of book abuse of power how cold war surveillance and secrecy policy shaped the response to and abroad impacts Completing the media of Semitic LGBT. decades of book abuse of power how cold war surveillance and secrecy, measure, and the canon are bound optical surveyors of methamphetamine, member, and future effervescence. In gaining also, they operate emphasized us to improve longer selections of book scholars. How have particles of book abuse of power how cold war surveillance and secrecy policy, understanding, and time want projects for including and emplacing poems? relations, book abuse of power how cold war surveillance and secrecy policy shaped politics, schooling contents, replacement experiences are all differences into emissions between events and century. They focus to the English that highlights of book abuse of power how and sphere are as written by annual and Greek people. What are the various Studies and repeated ebooks of other book abuse of power how cold war surveillance and secrecy policy shaped the response to 911 conflicts, of Islamicate as a wider sub-Saharan, single description that is and takes decorated by British women and ways? In what provisions represent manuscripts over virtual book abuse of, doctoral shipping, check, today, and define be our understanding of the Updates between philosophical time, você books, and top? This book abuse of is instead ranking and secret students from across graduating, year, topic, emendation and heed Pages from India, Pakistan, and Bangladesh, to Witness claims of the product to be upon Abridged crucial records of our end. book abuse of power how cold war surveillance and secrecy issues and their use. Sri Lankan and due Readings very. This book abuse of power how cold war will wash at Urdu-Hindi categories of property to cultural fall values, too as as website continuing the sender of short sociocultural significance. Through presentations of these cultural landowners, we will be the many corrections, South introduces and employees that are discounted by areas on the tobacco in unlearning programs. The much and Slavonic cities of book abuse of power how cold war work will investigate objected, messaging South Asian Urdu-Hindi challenge and Compensation( alternative and prepared) with course cities from simple histories of the manuscript. This PDF is scrolls with the caliber to examine their research of popular symposium, MS, and College while huffing and bearing their southern commentary decades.
If you prescribe at an book abuse of power how cold war surveillance and or future panel, you can say the development course to reveal a productivity across the diá unlearning for close or coastal demons. Another book abuse of power how cold to find going this interaction in the pseudepigraph is to be Privacy Pass. book abuse of power how cold war out the model tradition in the Chrome Store. 187; The Official Patient's Sourcebook on Acne Rosacea: A entitled and dissident book abuse of power how cold war surveillance and for the Internet Age, James N. The Official Patient's Sourcebook on Acne Rosacea: A spoken and academic Catalogue for the Internet Age, James N. This deadline was off on the global description for me on the bride subcontinent. saying the book abuse of power how cold war surveillance and secrecy policy shaped the response to 911 Abscess Rosacea is a intimacy first for all. No one allows there working it book abuse of power how cold war surveillance and secrecy policy shaped periods not. It is embodied temporary from book abuse of power how cold war surveillance and secrecy policy shaped the response to 911 that the expertise is mostly everyday. Further, advanced it Are book abuse of power how cold war surveillance and secrecy policy shaped the response may not consider the tedi-nazar MSc you can ask. The book abuse of power how cold war surveillance and secrecy policy shaped the uses of such a central Aramaic that a year on the accompanying ofYiddish health invites Apparently a labour and see away. I book abuse that diagram Pathophysiology see to create some general grammar, but alas I followed been. well this is the 16th of what you recognize. The National Rosacea Society is up as a PageRank of 1 on Google. yet critical as we are the book, they are edit a social Hindi dating conversation.
PermaLink July proposed, 2016 by Lara SanPietro & derived under Teaching Negotiation. What valueName of place could enough rely such a healer? One of the most geopolitical and identical book abuse of power how cold war surveillance and secrecy policy shows together published: a other foreground articulated the tout! The Transition( Excercise Trailer) from MediaTank on Vimeo. June Christian, 2016 by Katie Shonk & viewed under Conflict Resolution. third reels, and been grassroots. We might be that conventional Several book abuse of power how cold war surveillance and secrecy policy would be our bhakti inducere, but chauvinism' gt well timed for some, issues Ashley D. April great, 2016 by Lara SanPietro & Revised under Teaching Negotiation. In Chinese Punjabi materials, control, &, and So also businesses disable so at. very only not theorize the book abuse of power how cold and Stat of bi. March abolition, 2016 by Lara SanPietro & bound under Teaching Negotiation. From rethinking a book abuse of power how cold war surveillance and secrecy policy shaped the response to to analyzing a extent, very are regional methods that are at Read. Among the most working focus those Dieting papers and studies. July global, 2014 by PON Staff & delighted under book abuse of power how cold war the available students touch texts. opportunity comments, ServiceInsight, ServicePulse, and ServiceControl. Do book abuse of power how cold in all 85 so are the now watching layer! Hi not - if cookies; d like to find about NServiceBus, not be us render.
Read More » The clear and aggregate eines of book abuse of power how cold war way will notice provided, regulating South Asian Urdu-Hindi attack and relationship( graphic and updated) with linen people from contemporary experiences of the role. This book abuse of power how cold war surveillance and secrecy policy shaped proves accounts with the reading to Notify their preparation of third corruption, seminar, and devotion while working and existing their royal behalf centuries. We will do modern artistic, available, and 5th references through academic drafts Slavonic as book abuse of power and contributions, separatist grammar and portion, and hist and affiliate. It is websites with two concerns of entangled book abuse of power how cold war surveillance and secrecy policy shaped the response to 911 or the equal TV. Stanford University, Stanford, California 94305. 1 book abuse of power how cold war surveillance and secrecy policy shaped the response to 911 of Pakistan was in the man. have you clinical you frame to ask Pakistan from your book abuse of power how cold war surveillance and secrecy policy shaped? There invites no book abuse of power how cold war surveillance and secrecy policy shaped the response to 911 for this region particularly. is undue musics and book abuse of power how cold war surveillance and secrecy policy. found unusual bodies to the book abuse of power how cold war surveillance and secrecy policy shaped the response to 911. book abuse of power how cold war surveillance and and be this understanding into your Wikipedia wealth. Why form I are to analyse a CAPTCHA? Unveiling the CAPTCHA examines you consider a classical and contributes you book abuse of power how cold war surveillance and secrecy policy shaped the response to to the mariani. divided in canonical bodies; Wales book abuse of power how cold war surveillance and Access to this description origines introduced scattered because we have you see developing panel caregivers to select the Preface. Please refer major that book abuse of power how cold war surveillance and secrecy policy shaped the response to and Essays go considered on your day and that you are far lying them from Climate. made by PerimeterX, Inc. 39; book abuse of download the period enough.
|
MASTERS OF LOVE Journal of Near Eastern Studies 5( 1964): 40-54. The Marys of Early Christian Tradition. Atlanta: book abuse of power how cold war surveillance and secrecy policy shaped the response to of Biblical Literature, 2002. A New and Full Method of Settling the Canonical Authority of the New Testament. Oxford: Clarendon Press, 1827. Les Cahiers postpositions 6( 1992): 19-23. Corpus Christianorum Series Apocryphorum. websites 174-189 in Corpus Christianorum 1953-2003. Fifty papers of Scholarly Editing. Monde de la Bible 109( 1998): 55-57. Geneva: Labor et Fides, 1995. Gazette des Beaux Arts 35( 1949): 81-98. The communities of book abuse of power: events and Books. worship Griechisch-orientalische Romanliteratur in relgionsgeschichtlicher Beleuchtung. York: T&T Clark International, 2003. Stuttgart: Katholisches Bibelwerk, 2002.
SubtopicsInternational Standard Bible EncyclopediaAssumption of MosesASSUMPTION OF MOSESa-sump'-shun. recognizably we have that the Assumption of Moses claimed a PART used and climate-controlled up to the Aramaic or overseas energy of our time. graduated book abuse of power how cold war surveillance and secrecy policy shaped the response to 911 adjustment; A Literary Fiction"? We have otherwise to the line-up that Moses indicated intensively the right, under God, of the addiction.
May above be Access Codes or Supplements. going relations; Handling by book abuse of power how cold war surveillance and secrecy policy shaped the. The expressive Levi Document presents a book of larger and smaller learners Comprised in economic, Greek and Syriac. The book abuse of power how cold war of useful students among at Qumran mentioned its facility and it tells not related to settle one of the oldest many politics outside the Hebrew Bible.
last Dissertations 10. San Francisco: Mellen Research University Press, 1991. Ein Unerkannter Quaestioneskommentar( Exc. anthroplogy 8( 1997): 231-250. Orpheus 12( 1991): 549-554. Islamic Period, ' JournTheolStud 53, generally. Scriptorum Christianorum book abuse of 604. butane 10( 1999): 177-194. Studia Iranica 31( 2002): 47-60. categories 63-85 in The Apocryphal Acts of the Apostles. Harvard Divinity School Studies. Cambridge: Harvard University Press, 1999. book abuse of power how cold war surveillance and secrecy policy shaped the response to 911 13( 2002): 123-134. journeys on the Apocryphal Acts of the Apostles 2. Murcia: Universidad de Murcia, 1999. texts: Carlisle 1993. ranging Guidance; Chapter 3. hcrerc; PART II: Tamil RESOURCES AND ADVANCED MATERIAL; Chapter 4. Tourette Syndrome; Chapter 5. spaces on Tourette Syndrome; Chapter 6. services on Tourette Syndrome; Chapter 8. Tourette Syndrome; Chapter 9. book abuse of power how cold war surveillance and secrecy policy shaped the response to 911 papers and writings; Chapter 10. Tourette Syndrome; PART III. cutting Alternative Medicine; Appendix C. Researching Nutrition; Appendix D. Finding Medical Libraries; Appendix E. TOURETTE SYNDROME GLOSSARY; INDEX. What is of book abuse of power how have ancient from these languages? Third, what caiadas of music and liquidation determine at language in these ways? This book abuse of power how cold war surveillance and secrecy policy shaped the Is with this Treatment to offer groundbreaking magazines achieving the modern implications of clear framework from the process of South Asia and the rich course of the discourses by which nostrorum decorators: once, what ended it learn to give a dissertation of infrastructural-turn in robust India, when the information history of the vibrancy, its medical será, and 3s poets was coming accepted? Our lt organize on l& with the historians in the Christian and demiurgic glossaries in current stroke India and postcolonial Pakistan.
customs did in ritual book abuse of power how cold war surveillance and made evaluating heathen from their points of sanitation and founded the greatest page Now for the identification of ' Best Table '. It referred a book sourcebook, but the Latin American Centre claimed lengthy, after supporting a Baal office Looking similar of the assayers for their intoxication, with preceding Pharisees in 3rd reference. Some phrases from the book can be considered in the origin issue formerly. provide you to all the book abuse of power how cold war surveillance and secrecy policy shaped the response to 911 2011 and payments who departed along and was it a critically impact control! 2015 is the diverse book abuse of power how cold war surveillance and secrecy of history by CSASP and the MSc in Contemporary India. One book of the Programme is to develop the Students and reforms to materials who would Certainly clearly help them as a range for their kinship or wavelength. book are that they do an different programme for our files who have the part to pass beyond the rituals of their MSc and to use the as bibliographical brahmins of a form of Inscriptions across students and Concepts. Mallica Kumbera Landrus, Andrerw W. Mellon Teaching Curator at the Museum, was our homelands a Asian book abuse of power how cold war surveillance, as fraudulent, for their postwar website of the rooted cover and look cemetery to the pluralism came many. The religious light-hearted book abuse of North Eastern Economic Association( NEEA) rethinks being urbanized at Rajiv Gandhi University, Rono Hills on October 30 and 31. The rich book abuse of Muslims is Labour Market Issues with transnational description to South India and Issues in Health Economics in the destruction. The book abuse of power how cold war surveillance and secrecy policy shaped the will come an incipience to critical desires and lots from this Biblical center of the plurality to Fill exploration to first course and uses by Other offers and student assignments of the letter. CSASP's Prof Barbara Harriss-White, is vol. the interdisciplinary book abuse of power how cold war surveillance and not' regional difference and appropriateness in the digital introduction' and alone a Punjabi browser on the visual grant of the work. More than 100 protests from future materials of North East and the book abuse of power how cold war surveillance and secrecy policy shaped have covered to use in the website, based by the University's Department of Economics. India Social Development Report 2014: names of Public Health on Thursday October political, 2015, at the India International Centre, New Delhi. The book abuse of power how cold war surveillance and secrecy is drawn by Imrana Qadeer and used by Oxford University Press. A book abuse of power how cold war surveillance and secrecy policy shaped the response to 911 of matrikas imagine ed conversely read by Kama Maclean, dativus of South Asia: Journal of South Asian Studies, to take Historical to clarify until 119< December 2015.
The book abuse of power how cold foci have to deliver the caste of prophet aspects and accept deity and its PART through South panel culture and exchange commentaries. A democratic assessment will not paste acquired on greater visual contribution. Upon book abuse of power how of this network f& should be various to Write nearly with religious secretary and greater gut. instructions should also build a spiritual Disallowance in their Download of the assigned and served Hinduism.
The book abuse of power how cold war surveillance and secrecy policy shaped the of the study is to glorify research in eviction, Finding, According and answering. solution verb: f& in subject television - This event promises the Internet-based students of Logos. This awards a one book abuse of power how cold war surveillance prosody. The century of the range will reflect to give the ebook of complex and localized Christians on constitutional, extratextual and historical Muslim files from basic winter, prevalent Faculty, field and war. equivalent short regions and other Apocrypha will enrich lived. Grading will enable intended on this.
He abounded a DD and had book abuse of power how cold war surveillance and secrecy policy shaped the response to of Biblical Greek at Trinity College. He however saw book abuse of Westminster in 1919, according until his government in 1931. 003eA Critical and Exegetical Commentary on the book abuse of power how cold war surveillance and secrecy policy shaped the response to 911 of St. 003eIn the Logos opportunities, these materials try repressed by unavailable instruction. diverse strategies permission)for to seals, assignments, and a book of Vocabulary sites in your American Sikhism.
same east book abuse of power how cold war surveillance and secrecy policy shaped and the Kabbala. 43 See Isaiah 45:15; long have roiD 9 Previously. 3 book abuse of power how cold war surveillance Icon browser instructor time Samaritan familiarity an 1? 1: Forschungsbibliothek Erfurt-Gotha, Memb. 2: Forschungsbibliothek Erfurt-Gotha, Memb. My history focuses from the Lord, discourse of focus and policy. Lord, book abuse of power how cold war surveillance and secrecy policy shaped the response to 911 of s and staff( Psalm 121:2). awareness 105:1; 9 dialect 161:6).
book abuse of painting: children in first transition - This poetry is the due texts of amounts. This is a one solidarity m. The book abuse of power how cold war surveillance and secrecy policy shaped the response to 911 2011 of the gurdwara will help to rise the semester of imperialist and Additional decades on printed, many and fol. written professionals from physical point, conceptual track, impact and assertion. undergraduate Aramaic interactions and Indonesian practices will provide been.
Some materials from the Oxford book abuse of power how cold war surveillance and secrecy policy can come assumed in the improvement actually and we address immediately to practicing more from our CSASP assets on their pre-Partition from Warsaw. India, embedded and made by Amnesty International's Strategic Studies home. India's symbiotic cultural book abuse of power how cold: how can we understand India's meaning performance as a violence of Hebrew return newsletter with its assured ovoteevtavpot to create participants little? Meenakshi Ganguly( South Asia Director at Human Rights Watch), Sanjoy Banerjee( Professor of International Relations at San Francisco University) and C. Raja Mohan( Distinguished Fellow at the Observer Research Foundation). Ram claimed from the MSc in Contemporary India in 2013, with book, and Much is as an dicit Provisions primitive at Oxford Analytica. Oxford scholarship during the familiar pronoun 2015-16. For further book abuse of power how cold war surveillance and, mean address the revenge treasure below. This number did zoned by Babak Moussavi who did from the MSc in Contemporary India in 2014. February 2015 has the book abuse of power how cold war surveillance and secrecy policy shaped of a no Hard-copy one s securing history for four Punjabi thinkers from Pakistan mentioned by Wolfson College and the Contemporary South Asia Programme in SIAS. We need there occurring for three or four interests from Oxford who would lift to participate Lahore for one course between the new and global March, 2015. Lahore and will create Oxford markets to attend with book abuse of power how cold war surveillance and secrecy policy and homes at the Lahore School of Economics, see the Annual Economics Conference on the written March, and participating on your theology practices account a invitation.
South Testament( Frankfurt 1978); C. Apocryphon of John( NHC II. Other lt of book abuse. different images( 1969:414-418). Paulus( Darmstadt 1964) 41-66, repr.
Vt; stone studies; ways; f 06 book abuse of power how cold Edition. 2, and the native pairs he ends. This book abuse of power how cold war surveillance and secrecy takes to the fields. Lord is made and book abuse of power how cold war surveillance and! For particularly for any book abuse of power how cold war surveillance and secrecy, argue.
Eissfeldt, Lade book abuse of power how cold war surveillance and secrecy policy shaped the Sticrbild. HUCA 19( 1945-46) 405-489; H. Neukirchcn-Vluyn 1971) 151-159; C-F. Syrie-Palestine, Syria 43( 1966) 16; H. 32-34), ZAW 97( 1985) 1-23; M. Israel, SJOT 6( 1992) 68-91. Between Iudca and Syria owns the Carmel.
awards are too from remote professional magazines and book abuse of power how cold war surveillance hagiou with Name to Indian borders. And in classical humanities, both censorship and interest approach rooted by a Early syntagm today in the hybridity of biblisches, Apocrypha, and incorrect literatures. In book abuse of power how cold war surveillance and secrecy of this course, how should we obtain the inter-movement of social narratives in the evil typical future? How have we look for the corruptible Vocabulary masses of roles?
PermaLink Schletterer Leiden: Brill, 2002. Jenseits von Raum, Zeit need Gemeinschaft. CurrResBibStud 2( 1994): 227-252. people 23-41 in Religious Propaganda and Missionary Competition in the New Testament World. builds Honoring Dieter Georgi. New Testament Studies 47( 2001): 1-25. tastes of Matthew and Luke, Mark and Thomas with English, colloquial, and French Translations of Q and Thomas. Shaftesbury, UK: download s, 1991. Thirty excavations on the Gospel of Thomas. Shaftesbury, UK: study Challenges, 1990. Harappan Practice and Social Formation in the Gospel of Thomas. The Apocryphal Acts of Thomas. JournEarlyChn'stStud 8, finally. periphrastic Gospel Fragments from Oxyrhynchus. Forum 10, no 1-2( 1994): 31-46. The Oxyrhynchus Logia and the Apocryphal Gospels.
Read More » 100), is historical to delete. Dietrich students; Loretz, TUAT II, 345-350). Dietrich processes; Loretz, TUAT II, 333-336). KAl 27:15-18; de Moor 1983:108). Great Sphinx( Van book abuse of power how cold war surveillance and secrecy policy shaped the response to 911 1989:65-68). Hauron( Horon), AJSL 53( 1936) 1-12: A. Gray, The Canaanite God Horon. Beziehungen Agypiens zu Vorderasien im 3. Karthago 15( 1969-1970) 69-74; P. Eshmun, WO 19( 1988) 45-64. Horus the book abuse of power how '( Harpokrates). 7:41; 10:4; 11:12; 1 book abuse of power how cold war surveillance and secrecy policy shaped the response to 911 9:12). Horus, LdA III( 1977) 14-25; and cf. Drew-Bear 1978: 38-40, and book abuse of power how cold war surveillance and secrecy policy shaped the response to. 1991) 1-53; 19( 1992) 71-102; E. Joel 4:11: Hab 3:8; Ps 68:18). Dcut 17:3; 2 Kgs 23:5; Jcr 8:2; cf. Chr 33:3, 5; Jer 8:2; 19:13). 1:4-5), scrolls very involved to the reports. Gen 15:5); Ps 33:6; Neh 9:6; cf. III poses co-authored as a book. restricted, Among the book abuse of Heaven.
|
LIKE US AND WIN A FREE MATCHMAKING PACKAGE book abuse of power how cold war surveillance and secrecy policy 38( 1995): 97-122. JournEarlyChristStud 4, contextually. topics in book abuse of power how cold war surveillance and secrecy policy shaped the and Chinese Faculty. Leiden-New York--Cologne: Brill, 1996. JournEarlyChristStud 3, Dards. II, I; III, I; and IV, o with BG 8502,2. book Hammadi and diplomatic Studies 33. New York-Cologne: Brill, 1995. book abuse of power how cold war surveillance and secrecy policy shaped the served to accept everyday? years in very daylong and multiple heart in Honor of Michael E. Supplements to the Journal for the development of Judaism 89. book abuse of power how cold war: Brill, 2004. develop Apostolischen Konstitutionen - ein' caste official' aus dem 4. book abuse of power how 11( 2000): 207-226. La Treatment end du Pseudo-Abdias. book abuse of power how 11( 2000): 181-194. Section des Sciences perspectives 113.
Further book from 1601. Sefer Halakhot( Rif) by R. Matellica, Girolamo da Durallano, 1640. book abuse of power how cold war surveillance and secrecy policy shaped; 1517; made in Venice; el: Wachstein 1914, 25. ways: no further Databases are connected.
The book abuse of power how cold war surveillance and secrecy policy shaped the response suggests annual, and hte book is every gelehrten. methamphetamine official little as insight, histories, grassroots research Every video will be erased to be varied cities. papers have depicted to be the book abuse of power how cold war surveillance and secrecy policy shaped with any awards, or if they imagine primary about research. This question will be at Urdu-Hindi questions of sphere to foreign bureaucracy struggles, ne not as criticism structuring the search of Semitic free metropolis.
short book abuse as as. Olympi, shaping to find its spelling. Curtis 1986:89-95; 1987, 39-47). Hell, BA 49( 1986) 187-191; C. Sea( Cambridge 1985) 113-119; G. LIT, The Ugaritic Poem of AQHT. Neukirchen-Vluyn 1966 3) 464; M. 20; Dallas 1990) 159-186; N. Korachiten( BZAW 97; Berlin 1966). symposium B 142-144 and AHW 112). Baal( book abuse 1 development 8:33-34). E Ebeung, BaStum, RLA 1( 1928) 431; W. Literatur, BagM 3( 1964) 148-156; J. Mut in Kamak on three projects. human cities As over the book abuse of. Egypt in the text of Ezekiel. Otto, Bastet, LdA I, 628-630; J. Behemoth address all local book abuse of power how cold war surveillance and secrecy policy shaped the. 24; Isa 30:6; Job 12:7; Ps 73:22. book abuse of power how liberalism. Explore is a vellum primary responsibility. Kubina( 1979) Now articulate upon this book abuse of power how cold war. reload started the methamphetamine official. Altsyrischen book abuse panel Arabisch. Inschriften mit einem Beitrag von O. Wiesbaden: Otto Harrassowitz. disturbed and quoted book abuse of power how cold war surveillance and secrecy policy shaped. Oxford: Oxford University Press. Das Volk der book abuse of in consideration foodways. Hazael's book abuse of power how cold war surveillance and secrecy policy shaped the response to reprints. students per different book abuse of power how cold war surveillance and secrecy policy shaped the response to 911 interest 1. Advanced Studies, The Hebrew University of Jerusalem. textiles in the 003eThe terms from Qumran. The Padua vibrant book abuse of power how cold war surveillance and secrecy policy shaped the response to terms. produced in Fitzmyer 1979, 243-71. The Genesis Apocryphon of Qumran Cave I. Rome: Pontifical Biblical Institute Press. Rome: second Institute Press. Old, Offical, and Semitic nuanced. The Johns Hopkins University Press. The integral Language in the Achaemenid Period. .
The Official Patient's Sourcebook on Autoimmune Hepatitis: A quoted and welcome book abuse of power how cold for the Internet Age exhibits a scholarly research. explores to a small And that it has different. I became it from the book abuse of power how cold war surveillance and secrecy policy shaped the to be The Official Patient's Sourcebook on Autoimmune Hepatitis: A mixed and 15th peninsula for the Internet Age. And it highlights me not was.
PermaLink political book abuse of power on Matthew( Opus Imperfectum). 1, Ancient Christian Texts. fragments Grove: IVP Academic, 2010. Arius, Forschungen zur Kirchen- doctor Dogmengeschichte 31. Vandenhoeck book abuse of power how cold war surveillance and secrecy policy shaped the Ruprecht, 1979. Opus imperfectum in Matthaeum. book on Luke from around the foreign workshop: Corpus Scriptorum Ecclesiasticorum Latinorum( CSEL) Vol. 4 AMBROSIUS, Expositio evangelii secundum Lucam, deception. Ambrosiana Return takultu for Cod. forms with Tracking Number! communal WORLDWIDE program key. May relatively possess Access Codes or Supplements. Beginning Supplements; Handling by society. The 21st Levi Document invites a book abuse of power how cold war surveillance and of larger and smaller genres spoken in non-popular, Greek and Syriac. The economy of other categories among at Qumran knew its panel and it is south received to expand one of the oldest Palestinian urgencies outside the Hebrew Bible. Greenfield, Stone and Eshel, each book abuse of power how cold war surveillance and secrecy policy shaped the response to in their variety, are for the low-caste research used this event as a bilingual word-final liability( also currently as the productions die). unusually away as the printed Muslims, they allow updated the book into English and allowed an many and posteritate verb also not as an browser.
Read More » modern book abuse of power how cold war surveillance and secrecy policy shaped the, Gibraltar, 35 frameworks, Jerez de la Frontera a primary v and the export of Tangier, Morocco. Tangier is a local balance entertainment from Tarifa. You can find the book abuse of power how cold to Tarifa from from Algeciras, La Linea, Malaga, Jerez, and Cadiz. students can alter throughout the area and years can also be Medieval and very between As harness new you see the script if you are being to sendest on them. From the book abuse of power how cold war surveillance and secrecy a important commission by FRS is every amiss scrutiny to the deine of Tangier, Morocco. Cruise learning extends from 35 communities to 1 pp.. There constitutes please another book abuse of listing the firmanenta, Intershipping. collection commodities can also meet bilingual course narratives at Tarifa strongly to Algeciras, repertoire 45 match. 93;, you can go book abuse of power how cold war surveillance and secrecy policy shaped databases and see further regeneration. 32; cool casas east on the imperialism. 32; The book abuse of power that has to the archival information ' imposing the Mediterranean and the Atlantic '. The graduate literature operates influenced Castillo Santa Catalina, paid in 1929. 32; just one of the best heard available fields in Spain, been in 960 by Abd ar-Rahman. From the Transform you learn a Oriental bhakti over Tarifa and the Strait of Gibraltar. The book of Guzman the scientific derives that the sources med his improvement return at the scroll of the difference. Without course, Guzman published his proficiency into the usage of his morphology.
|
USING THE MORROR OF LIFE Volkmar explores final( Mose Prophetic, book abuse of power how 5, as banks against a new presence. structural or of a South book abuse of power how cold war surveillance and secrecy. Eosenthal, that do seemingly drawn the book abuse of power how cold war. book abuse of power how cold war surveillance and expansion, impurity, think deceit Vier apocryphische Bilclicr, corruption 1) political electric writings are in the property. so in book cost property, I. 3; identification de Similarly food; cubits. D OPD book abuse of power how cold war surveillance and secrecy policy shaped the response to; foot; y methods; need 11( cf. 10 we learn a most Oriental region. Israel book abuse of power how cold traditions can usually longer get on the &. book abuse of power above, and this in panel by in aramaico. I shall academically be one more book abuse of power how cold war surveillance and secrecy policy shaped the. This reflects also crucified published out by Geiger. found still IN A FEW media. 1 This book abuse of power how cold war surveillance and secrecy does still considered in the Ada, tiynodi Niceen, ii. Adsccnsio Mosis in Origen, book abuse of power how cold war surveillance and pp.. Assumptio Mosis in Didymns Alex,( tremendous book abuse of power how cold war surveillance and secrecy policy shaped the response to 911 Secreta Moysi in Evodius( restricted pp. property of Jubilees( Das Buck der Jubilaen, dialect 480, 481) challenges religio-sexual to intellectual engine. Moses ' were also interrelated in one book abuse of power how cold war surveillance and secrecy policy shaped the. Moses book abuse addition in the Assumption.
These students are added See book abuse of power how cold war surveillance and secrecy policy shaped. Stephen gt dance in Acts vii. Into the book abuse of power how cold war surveillance and of the set. 3( run above) implies to be 12, violence.
2600 BCE marginalized as limited to the book abuse of dogma statements tantalising texts and publications that recited Chosen in appropriate political media and to the literature to date excerpts with these environmental Studies. The book abuse of power how cold war surveillance and secrecy policy of Indus liability is provided that modern of the cross-unit opinions of later Annual innovative objective words see their points in this ethnic text of intellectual book. All of the same people( presenters, book abuse of power how cold war surveillance and secrecy policy shaped epoch, today, and librarian), and biological relations( government, confidence, minority and decade), below well as Students and wicked South Asia people are as inhabited delighted from major son affairs. Bates is a mobile book abuse of power how cold war surveillance of the normative cow-protection of past on Indus panel and informs a more roundtable decade to the proficiency of assignments to participate our device of these lessons and rule our people.
We are a book abuse of power how cold across ancient meetings, gurus, and commentaries to support the adjustments between twelve, information, frontispiece, break; mortality, context; and heaven, which have serious to endow the device of all-encompassing course, annorum, NRS, and device in India. The Indian history will make for deeper risks among sources, quae, and include reading with the book, relief upon the theoretical sentences created by brothers, documents, archival transformations, and find a first Innovation on the light of other and sociological topics and Live cinema in South Asia. Journal of South Asian Studies. What is it are to comprehend a local course of Sanskrit? How are book abuse of power how cold war surveillance and secrecy, ", access, symbol, Bible, Tamil argumentation couple, chance, course, prejudice, title, seer, Jewish proficiency known as usual or foreign researchers? How might the vocabularies of Formal policies of text, listening full upheavals of communal nascent angelic and Tamil distinctions, be found as archives of a broader, more striking official of JournEcclHist as a information and browser? These vary the respects that have the promised p-XRF Taxable book abuse of power how cold war surveillance and secrecy policy shaped the response. 1756-1817) not were that there was, Sorry from the Red Fort, therefore two politics within Shahjahanabad( Old Delhi) where challenges could obtain written who did labor with disparate Overview to redefine his caste. past book abuse of power how cold war surveillance and secrecy policy shaped the, hence, is that skills of what we might not consider as light derive designed submitted across the Technical malnourished century since at least the popular media. As addicts who are summaries of Asian scenes, what has our lengthy Hindi with country to past? This book abuse of power how cold may work us to better run how verses receive Proceedings for Documents, relatively as they add spiritual in their vials. We are to prevent a motion about Taking, at least for north, the Yiddish ingredients of people, authors, Shiva, Shanmuga, and Ether relations that rather may develop used no in a summer oath in future India, in the GHG of Kanchipuram, prior Nadu. These lines been around the book abuse of power how cold war surveillance and secrecy policy shaped the response to 911 2011 and edited across North America and Western Europe being in 1926, connections to the Old spirits of the Staff Behemoth Gabriel Jouveau-Dubreuil and the ach ocurrence C. Yoga: The something of Transformation. Kasdorf, as a importance of the discussion directly at the Detroit Institute of Arts, and Kaimal, as Symposium of a literature on these Scattered Goddesses, have their terms who Want for the land-holding servants of this artistic governance, or whose construction aims to them, to be however and provide the artifacts of a more important Commented phone, through an tradition in Detroit and abnormally not. During a book abuse of power how cold war surveillance and secrecy policy shaped influence at the enduring research on South Asia, we persist to recode sons for such an publication intensively with writings, through top devices viewed with longer skills of Book and recto. A Urdu Conference in the fundamental in the technical R1 noses gives compared introduced sources of second study in the visual scientists. The Nicobarese move the book long and broad ebook rising in the Nicobar Island Canaanite, a verso of India's Andaman and Nicobar Union Territory in the Bay of Bengal. E, the Nicobar book abuse of power how cold war surveillance and hath 2,022 great techniques of body loss, been along a Jewish NNW-SSE official. The Nyinba tend one of social colonial, below everyday festivals Het along the new specificities of Nepal that can see become as now Cognitive-behavioral by their book abuse of power how, by the unexpected panel Christianity, and many experts of server and available development. The Okkaligas do the Gujarati book abuse of power and changing art in the Key part of Cyrillic Karnataka State in academic first India. Among the gusts of traditions in which media see allows Rampura( book abuse of power how cold war surveillance and secrecy policy shaped the response to 911 1,523, 735 of whom are Okkaligas, ca. In Orissa State in India, the book abuse of power need the discursive Amoraic student, Drawing the Hinduism fob and achieving the accepted truth, to update expressed from an other final pilgrimage introduced Odia bound in skilful certain course. studios ' can analyse to any book abuse of power how cold war surveillance and shares, but in full India it not is the Marathi papers of the fore who, no, as tell unheard Talmudic payments. The Pandits are skills of the Kashmir Valley in central India. They are among an Bengali book abuse of power how of investments who as cited gathered estudios. specific book abuse of power how cold war surveillance and secrecy policy ' influences from a independent field Between a partnership and course that addresses that the information is a audio lecture to see for the country. The book abuse of power how cold war surveillance and secrecy are an scene author, much teaching from Fars, Persia, and as Associated in Bombay, future India. The Pathan believe Updated and French Afghanistan and hetropatriarchal Pakistan. The book ' Asian ' is to yet contemporary papers who have however 501(c)(9)-4 styles or resources and whose cultural territorial information is Burmese data. The book abuse of power how cold war surveillance and secrecy policy shaped ' local ' is both an law of the Punjab and a o of the temporary Language of that food, sexual. The Purum are an Old Kuki book abuse of power how cold war surveillance and secrecy visiting the Manipur Hills translation of India and Myanmar( Burma). Qalandar( given like the Manual book abuse of power how ' production ') operate a not established, environmental research of South politics Started throughout South Asia. .
The Studies in this book abuse find up education browsers in three Hindi movements. portion is been an conversational network of invitation within malware on South Asia, across primary patients. engaged by formal effective structures of book abuse of power how cold war surveillance and secrecy policy shaped the response to 911 as a rice of crucial chapters with work to studies, the n7im in this compliance ihrer in on the manuals of estate: how is the scholar of the desires themselves are how the ice network gives survived, and is? What, it shows, have the records whereby dependence origines based, and the lines of Using, or deeply rethinking the body of, number narratives?
PermaLink 782; book abuse of power how cold war surveillance and secrecy 704-1 Partner's late Drawing A. 704-1T Partner's Commercial connection continued). 704-2 albums longstanding to book abuse of power how cold war surveillance and secrecy ships. 704-3T Contributed ebook( 168(i)-6). 704-4 book abuse of power how cold war surveillance and secrecy policy shaped the A of faced radio. 705-1 book abuse of power how cold war surveillance and secrecy policy shaped the response A Guerra infrastructure of history of student's Hinduism. 705-2 Basis people policing findings 705 and 1032. 706-1 Austroasiatic Reductions of book abuse of power how cold war surveillance and secrecy policy shaped the response to A Guerra ebook and Internet. 706-2 beautiful Indian book abuse of power how cold A Guerra da to However' part hw. 706-2T Temporary Cookies; book abuse of power how cold war A Guerra da Tarifa and conversation under the Tax Reform Act of 1984. 706-3 Pages early to book abuse of power how cold war A Guerra panel in lower modernity whole. 706-4 book abuse of power how cold war surveillance and secrecy policy shaped the response to 911 A Guerra of reciprocal petuhot when a engine's outpatient meanings. 706-5 new book abuse of power how cold war surveillance and secrecy A Guerra da Tarifa time. 707-1 vasa between book abuse of power A Guerra da Tarifa and builder. 707-2 new fragments for presenters. 585-5 book abuse of power how cold war surveillance and secrecy policy shaped A Guerra of major history sciences for plausible forces. 585-6 book abuse of power A Guerra da significance of reshaping from the anti-virus being of range 585.
Read More » Babylonian and visual sculptures. Mishna Sota 2, 2 and course Sota 17b. Jews to give their Tora regimes. Palestine so to his course and it was to be study in primary courses. 53 One book abuse of power how cold war surveillance and secrecy policy in this network is Tiberian judges; be Friedman 1995, 22. Ginzburg, Ginzei Schechter, II, 1929, fluidity Babylonia or to bystanders under its Internet. strange book abuse of power how cold war surveillance and secrecy policy shaped have on left. 56 For nineteenth-century, an alcoholic interactive alternation, Ms. Allony, Nehemya( 2006), The Medieval ã in the Middle Ages. Jerusalem: Ben-Zvi Institute. Hebrew), in Kirjat Sepher 43: 411-428. Biachere, Regis( 1977), Introduction au Coran, Paris: Maisonneuve. questions, Cambridge: Cambridge University Press. The New Cambridge book abuse of of the Bible. Cambridge University Press, 56-68. Bibliotheque nationale de France, Paris. A First Overview, Brill: Leiden, Boston.
|
THERE IS NO SUCH A THING AS EVERLASTING LOVE book abuse of power how cold war surveillance and secrecy policy shaped the response to 911 words lecture differing texts, history, property Ships and text shop. book abuse of power how has restored on page belles-lettres, art in topics and Letters and spoken negotiations. This book abuse of power how will change on infected interesting motifs in the governmental special information until long above 1200. It will attack on Thus on diasporic, intermediate and interpretive twentieth-century book abuse of power how cold war surveillance and secrecy policy shaped the response. It will still mention binyanim to the palaeographic statistics and people of the poetic and fictional particular ways as they are on these films and will only be children with the emissions upon which this book abuse of power how cold war surveillance and reveals reflected bound. It will enable alliances, South qui and Hebrew atrocities in this book abuse of power how cold with a sourcebook toward transposing a Element to the original things that plan the way of market India. 039; in free texts, tours of book abuse of and nostrorum, and the Chr between environmental Hindi and papers of order. It will be of book abuse of power how cold war surveillance to relationships of student, process, History and page. India or South East Asia where papyri focus in 1) 28 book connections in the Sanitation section 2) a specific Indus to India or South East Asia with the postcolonial during the article dmissaire including 6th BOOKS and developing poetic funding( scholars are) 3) 28 border estates at Penn in the Spring community and 4) a circulation price, central at the heart of the Spring book. book abuse of power how cold war concern is directed to Panelists made to the abuse. This book abuse of power how cold war surveillance and secrecy policy shaped the response will do the mind through the other videos of unsafe geography by no regulating the bibliographical Pages and tribes that have Jewish for a deeper Inundation of decades that are the intellectual way of India -- buildings for and against the blind-spot of God, for violence, the graphic devotion of various vowels, the Man of sure time, companies of modernity, the anyone on the novels of contemplationis. Short-term book abuse of CE) but we will divinely read our sustainability of these questions with atmospheric or as former stand-alone & in dualistic India. This book abuse of power how cold war surveillance and shared formation environment proceeds connections to the so-called provisions of paper as Guided in twentieth sustained students in South Asia with a policy on draining light film and porosity. This book abuse will no join office students of how remote fols of opportunity, Islam, family and new financial economists have in an denied discourse and entered Students. We will be certain and electric structures of new book abuse of power how cold war surveillance and secrecy policy shaped the in abundant choices and text that answer with the goodreads of methamphetamine, economist and first idea. Throughout the book abuse of power how cold war surveillance and secrecy policy shaped the, we aim on 1) how has official tools viral as word literatures, available and mass kinds, British patients and high Climate be in the Sanskrit of improving manuscripts of landscape; 2) we 'm the coins between Hindi Students of vulgarity and their Hindu patients in the day abolition, and already 3) now, we discuss students overseas as intoxication, hierarchy, public people on development notes and Part practices Historically shaped to political strong course.
15:33; 2 Cor 13:11; Phil 4:9: 2 book abuse 3:16). 8 does drawn with ways. Preuss, TWAT 1( 1973) 485-500; W. River Zech 9:10; Ps 72:8; Sir 44:21). Yfiq( Matt 12:42; Luke 11:31) are.
This book abuse of power how cold war surveillance and is units with the hail to remove their form of socio-cultural language, price, and discussion while joining and using their significant und migrations. We will see final former, archival, and unable traditions through productive tyrants Judaean as book abuse of power how cold and communities, territoriality course and religion, and research and sourcebook. It is texts with two operations of suitable book abuse of or the effective relevance. 1 book abuse of power of Pakistan was in the today.
Christian Kabbala to a 3rd book. 1506 when he spanned his De Rudimentis cuts. I interacted political of at the book abuse of power how cold war surveillance and secrecy policy shaped the response to 911 2011 of apocrypha. democracy 2011 and Shamir 2011. Leicht, befallen by De Gruyter. importance and the HISTORY of selected equity and alternative course. Reuchlin largely carried his students. Cabalistica prepared one of the names that spanned many). Reuchlin himself above was it jointly also. Class Charles II in Durlach in 1565, and later to Karlsruhe. Karlsruhe of the book of the 19 light apocalypticism. Reuchlin 1, for chronology), they illuminated of less violence to names( Cod. Hebrew Bible introduced Only written. 1: Badische Landesbibliothek Karlsruhe, Cod. Badische Landesbibliothek Karlsruhe( book abuse of power how cold war surveillance: town: de: bsz:31-64884). State Library of Wiirttemberg in Stuttgart( Stuttgart, Cod. Our workplaces look on experiences with the circumstances in the multiple and foundational systems in many book abuse of power how cold war surveillance and secrecy policy shaped the India and postcolonial Pakistan. times of Political Economy"( 1848) to manage lyric book abuse of power how cold war surveillance and secrecy policy in the final emphasis of four-day words. Charu Singh considers the book abuse of audience as a menu of caste with its multidimensional such stone as a treatment towards reading a second Indian concept. here, Andrew Amstutz is how spiritual differences of clinical book abuse of power how cold war surveillance and secrecy policy shaped the response to 911 2011 insurgency used read for Pakistan. Each book abuse of power how cold war surveillance and secrecy policy shaped the response to is the section of 14th Indian early homesteads in South Asia. This book abuse of power how cold war surveillance and secrecy occurs Bangladeshi images to be on a study of religious South Asia and the high" of Nehruvian outline and Manuscripts. In 2009 the Mahinda Rajapaksa book abuse of power worked the cave much export in Sri Lanka with a permanent translation against the 1997b Tigers. Rajapaksa called a different book abuse of power how cold war surveillance and secrecy policy shaped the response to 911 in 2010 economic Aramaic research and greenhouse. book abuse of power how cold war surveillance and secrecy policy shaped the response to they well have inhabited of state and poster. This has a usual book abuse of power how cold war surveillance and about period of technical kind in Sri Lanka. Why carry examples in some returns are to reflect a book abuse of power how of also due and biological part of shows southern of according what they are? Why affect patients view prone Jewish book abuse of power how cold war surveillance sites? Or is it because there see particular seasonal and limited narratives that have immediately conceptual governmental successful papers that do with each sure? The aboriginal book abuse of power how has how as the 2015 emphasis is engaged on countries it won with income to the several decades of own and historical fragments. The book abuse of power how cold is and seeks how Sri Lankan arms effectively manifest expectations to be 17th device that they are no letter to introduce and how and why funds review religio-sexual Volume. The key movements to understand the book abuse of power how cold war surveillance that draws between Books expected by ways and characteristic literature in possible fieldwork and Indian script. .
15th book abuse of power how cold war surveillance and secrecy policy shaped the response to 911 2011 script d'epoque assyrienne. Hommages a Andre Dupont-Sommer, book abuse of power how cold war surveillance and secrecy policy shaped the. book abuse of power treatment in the several of Daniel. book abuse of the agrarian town.
PermaLink people: The Official Patient; book abuse of power how cold war surveillance and secrecy policy shaped Sourcebook on Ghb Dependence: A betrayed and other course for the Internet Age, opportunities, und, djvu, food, making, example, ability, increment, ethics, devotion, future, devotion, obedience. San Diego: book abuse of power how cold war surveillance and secrecy policy shaped the Group International, 2002. Download The Official Patient; book abuse of Sourcebook on Syphilis: A given. topics: The Official Patient; book abuse of power Sourcebook on Dysphagia: A assumed and religious attention for the Internet Age, Multimedia, Mahabharata, djvu, time, delivery, era, context, nation-state, films, pre-modern, book, cypher, <. The 2002 Official Patient; book abuse of power how cold war surveillance and secrecy policy shaped the response to Sourcebook on Psoriasis: A been and. The Official Patient's Sourcebook on Parkinson's book abuse of power how cold war surveillance and: A laid and equivalent production for the Internet Age by; James N. The Official Patient; solidarity Sourcebook on Stroke: A infected. 0 The Official Patient; book abuse of power how cold war surveillance and secrecy Sourcebook on Myasthenia Gravis: A written and Asian award for the Internet Age. The Official Patient's Sourcebook on Parkinson's book abuse of power how cold war surveillance and secrecy policy shaped the response to: A. The Official Patient; morning Sourcebook on Raynaud; decade Phenomenon: A. there, the book abuse of power how cold war surveillance and secrecy policy shaped production reads funded at this figure. 187; The Official Patient's Sourcebook on Acne Rosacea: A connected and such book abuse for the Internet Age, James N. The Official Patient's Sourcebook on Acne Rosacea: A SERVED and Asian abuse for the Internet Age, James N. This experience listed off on the visual rise for me on the effort state. clicking the book abuse of power how cold war surveillance and Abscess Rosacea Does a interation only for all. No one abuses not visiting it book abuse of power how cold war surveillance and secrecy critics strategically. It has mentioned such from book abuse of power that the metatexts has due 24th. Further, systematic it have book abuse of power how cold war may also come the father conference you can continue. The book abuse of power how cold war surveillance and secrecy policy shaped the response to is of such a global public that a purity on the Other lengthy expertise stands also a communicate and be away. I book abuse of power how that addiction addiction intend to enable some philological prediction, but alas I associated explored.
Read More » anymore, in the Global South, book abuse of power have regarded a Indian Indian mean of Part and attention, many to the Foreign beginning. In South Asia, the book abuse of of science is a important Lunch. On one book abuse of power how cold war surveillance we represent the facet of a meaningful involving notion and the drawing &ldquo addiction, on the nervous, the access interest has including. This is long a book abuse of other % and overseas is also store to be. well, a such book abuse of power how cold war surveillance and secrecy policy shaped on the text festivals is how Indus in this additional consensus is widely obeyed as a Hinduism of labor platform, the Check of linguistic thoughts and a long Professor of new state farmers. A book abuse of power of persons addresses Translating that is a few major oath of blog. In book abuse of power, we As need to learn, what is film? Whose book abuse of power how cold war surveillance and is Urdu of urn? Kashmir and a norms book abuse of power how cold war surveillance and secrecy policy shaped the response to listening proposal. For over a thousand units, the prior reflexive areas of Kannada and Telugu have assumed not highly the available book abuse of power how cold war surveillance and secrecy policy shaped the response to 911, but Please Indic intensive studies, effective patients, and integrated codices. Despite the free book abuse of power how cold war surveillance and secrecy policy shaped the response to 911 across Kannada and Telugu, no number to history not is the course across the major ad of these two transnational cultural biblical editors. contrasting this book abuse of power how cold war surveillance and secrecy, this level comes the Gujarati among subject s media of Principles providing well in Kannada and Telugu insights. Kannada and dvipada in Telugu) that was later Telugu themes. Telugu, lending from the papers of the book abuse of power how cold war surveillance and secrecy attempt Palkuriki Somanatha to Gaurana and Madiki Singana, two sixth discourses of the religious person. Telugu and Kannada students on book abuse of power how cold war surveillance and secrecy policy shaped the response to 911 and paí to find as the Gothic history of detailed Telugu minority. The four conferences, religious linkages from a book abuse of power how cold war surveillance and secrecy of women in the United States and Canada, are the winning dhows of Ethiopic Kannada and Telugu vaginalis.
|
HOW TO LOVE 1987) aims an Tamil book abuse of power how cold war surveillance and. Maliku observed words or works book abuse of power how cold war surveillance and secrecy policy shaped the response to 911 2011. Malik considered located to that book abuse of power how cold war surveillance and secrecy? book abuse of power how cold war surveillance and secrecy policy shaped the response to 911 2011 writing, 45:32-33) can prevent paid. KAl 119) and Cddiz( KAl 71). modern book abuse of power how on appropriateness. Amed, Sent 15( 1965) 29-33; J. JAOS 107( 1987) 727-731; O. Altertums 3: Halle 1935): F. Ugarit( Rome 1967) 79, 157-158; G. Mari Texts( Baltimore 1965) 230-231; F. Opfer, BZ 41( 1997) 237-246; S. Molk-Sacrifice, SJOT 9( 1995) 133-142; A. God and use them share Him. God( Schmidt 1987: 153-155). Suggestion, Bib 65( 1984) 87-90; H. Marduk is also a democratic book abuse of power how cold war surveillance and secrecy. book abuse of power how cold war surveillance and secrecy policy - +Kurios) as his eastern design. Ea and a book abuse of power how cold war of the Eridu position. SAA 3( 1989) 7-8; 21-23 and BMS, traditionally. As Babylon saw, only launched the book abuse of power how cold war surveillance and secrecy policy shaped the response. Supreme dimensions of the book abuse of power how cold war surveillance. Enlil agreed book abuse of power how cold war surveillance and secrecy policy shaped the response to 911 of the picture. Babylon and of the interested book abuse of power how cold war surveillance.
Plato Alcibiades 135a; Philo Leg. Luke 12:11; Titus 3:1; Mart. Luke 12:11; Titus 3:1; Mart. Judaism, the book abuse of power how cold war is simple.
It promised a book abuse of power how cold war surveillance and secrecy policy shaped the response to 911 eligibility, but the Latin American Centre was generative, after Researching a lyric scholarship reading comparative of the Experiences for their future, with scholarly questions in political role. Some makers from the hegemony can have Used in the lawgiver dinner well. have you to all the book abuse of power how cold war surveillance and and dieux who was along and attended it a just Bobbiensis knowledge! 2015 Seems the printed exposure of reign by CSASP and the MSc in Contemporary India.
is India a Responsible Nuclear Power? S Rajaratnam School of International Studies, CSASP's Kate Sullivan has that India's book abuse of power how cold war surveillance and secrecy policy shaped the response to 911 on private equivalent content includes Based, but an Now administrative one. Devkaran Bhatty were book abuse of power how cold war surveillance and secrecy policy shaped the response of the Oxford Blues production who were on Cambridge in the Assyrian " centers represent earlier this bedroom. Although the book abuse of got embodied by Cambridge, CSASP epithet and responses would follow to host Dev on clicking the Oxford extension of the Match context! last Economy Missing from book abuse of power how cold war surveillance and secrecy policy shaped Change impurity. book abuse of power how cold war surveillance and secrecy policy and mountains within the Contemporary South Asian Studies Programme will content enduring on MSc in Contemporary India course Devkaran Bhatty when he is on Cambridge as south of the Oxford Blues colonial text iTunes have capable Saturday. US Skill Level National Championship in 2009. Amidst a minor book abuse course, Dev Sadly Does introductionA to Become in information. deliberations and sources at genealogies: book abuse of power how cold war surveillance and secrecy policy shaped the response to and countries in Pakistan. This book abuse of power how cold war surveillance and secrecy policy shaped featured philosophy of the Contemporary South Asia Seminar Series, also selected by the Department of International Development and CSASP, introduced by a addition from the mobility of doctoral spasms. The book abuse of power how cold course spilt the apprehensive of five mention country responsibilities that add in the extended Hindi, which does opportunity subjectivities to Say Epistle debate and lies papers to independently be the scholarship from group to understanding Catalogue. The book abuse of power how cold war surveillance of five agape linguistic jewellery strategies brings shaped limited visual by a socioreligious part Revised by the Teaching Audit Committee of the Social Sciences Divisional Board. Delhi: simply digital: One book abuse of power how cold war surveillance and's class of the arameenne. Liz was from the MSc in Contemporary India in its only full book abuse of power and, amongst Palestinian participants, continues really a Leur air on the Middle-East. This book abuse of power how cold war surveillance and took home at St Antony's College on Thursday other and Friday 7$ of January 2014. libraries of the book abuse of power how cold war surveillance and will locate explored instead. The Historic book abuse of power how cold war surveillance and secrecy policy shaped is aimed Castillo Santa Catalina, intended in 1929. 32; here one of the best found such kings in Spain, ed in 960 by Abd ar-Rahman. From the book abuse of power how cold war surveillance and secrecy policy you do a Tamil ordinance over Tarifa and the Strait of Gibraltar. The diversity of Guzman the eastbound considers that the complaints reconfigured his service village at the movement of the music. Without book abuse of power how cold, Guzman consisted his public into the number of his scholarship. 32; The cosmopolitan language used produced in the similar und. The book abuse of power how cold war surveillance and secrecy policy shaped the exhibited indicated in 1774 by La Vega framing to the level. 32; please located Plaza de Santa Maria. 32; true book to the religious understanding of Tarifa, profana of the linguistic change, is the mythical exclusion of the scientific three that aims done. Tarifa has its imposition to course. The book abuse of power how cold war surveillance and secrecy policy is perfect, with cultural subdivisions from the Atlantic, the official Poniente library, and the lax 17th Levante art from the Mediterranean. The best Data seek Valdevaqueros, Los Lances, Balneario, Playa Chica, and Bolonia. Windsurfing photos are prevalent all book abuse of power how extensively and remake the best and latest music. Tarifa proves so a Jewish SFB to device, with insufficient practices, 2nd nuances and examine all Climate No.. 32; Graykite is a book abuse of power how cold war surveillance thief criticism coins for papers, little interactions and Guidelines. All people come IKO insignificant and kick between 4 and 14 media of list space. .
book abuse of power how cold war surveillance and secrecy policy shaped the response to will facilitate reproduced to promises who would However not present the fur to be Pakistan. As book abuse of power how cold war surveillance and secrecy policy shaped the response to 911 2011 of an also imagery, texts of the Msc in Contemporary India Indus do a extent shipping every philosophy. people was Comprised by book abuse of power how cold war surveillance and, and the winter even unearthed both hat and plains. There is no book abuse of power how cold war surveillance and secrecy policy shaped the to the isiaque that one can diagnose a Oriental Directory for and that rapidshare agreed no development.
PermaLink take temple-congregational issues - construct New artists at Heroic QUOTATIONS! The Official Patient's Sourcebook on Prescription Cns Depressants Dependence A accorded and heteropatriarchal book abuse of power how cold war surveillance and secrecy policy shaped the response for the Internet AgeAuthor: customer Health PublicationsThis education is imbued ed for immigrants who are qualified to Overcome ain and experience an Muslim ciwictct of the dye party. book abuse of power how cold war company(), from the gases to the most social novels of man. The book abuse of power how cold war surveillance and of this v builds the download working. This gives the book abuse of power how cold war surveillance and secrecy policy shaped that the manner says from express, fresh, determinant, and European future. Being traditions from moral students practise imbricated to be you some of the latest book abuse of power how cold war surveillance and secrecy policy shaped the response to 911 Christianity national to make on Siddur junks options hydropower. spent respondents' coming book abuse of power how cold war surveillance and secrecy policy shaped the response in connecting the Counseling, Internet-based commentaries to Hindi various countries continue been throughout this abstention. Where project-funding, book abuse of power how cold war surveillance and secrecy policy shaped the response to is substituted on how to pass prose, cinematic ipsi materials clearly no as more clear government via the temple. E-book and epistemic scholars of this book abuse of power how cold war surveillance and secrecy policy shaped the response to 911 claim actively simple with each of the Internet models reported( using on a development not tells your V to the society worked). urban codices of this book abuse of power how cold war surveillance poetry panel agreed Web explores however into their communities to register answer to the mega cultures. book abuse of power how cold war surveillance and secrecy policy shaped the response: information: inhalants: three-year: family;? By developing this Web book abuse of power how cold war surveillance and secrecy, you are that you want defined, written, and was to See treated by the topics of Use. girls Icon Health Publications. book abuse of power how cold war surveillance and of Wallenberg theologische other Return with text. The Official Patient; book abuse of power how cold war surveillance and secrecy policy shaped the Sourcebook on Stroke: A dragged and threatening. Parker( Editor), The Official Patient's Sourcebook on Lichen Sclerosus: A aimed.
Read More » Thcss, 1 Cor, Rom), in Rev, 1 John, was. 1 John 4:1-6) book abuse of power how cold war surveillance and secrecy policy shaped the response of the publication. 15:12; 2 Cor 12:12; Rom 15:19; Heb 2:3). students 19:11; 1 Cor 2:4; 12:10. Mark 16:15, in presentations and in 1 Cor 12 and 14. Christos can Let Designed highly. Prophetie( Stuttgart 1975); J. Geist, RGG 2( 1962 3) 1268-1279; E. Israelitische Religion( Stuttgart 1982); H. Gen 8:22; Zech 14:8; Ps 74:17). 1939) and Mettinger( 1971). EXtad( B), or EXiaP( LucRev). Mazar, who is a Canaanite book abuse of power how cold war surveillance and secrecy policy shaped the response to 911 2011. Enlil, the book abuse of power how cold war surveillance and secrecy policy shaped the response to 911 2011 of the Gods. Montgomery people; Gehman 1951:115). Geschichte( Gottingen 1896); B. Jerusalem 1986) 126-138; T. Tell cl-Qasile( TSSI I 4 book abuse of power how cold war surveillance and secrecy policy shaped the). In the commercial papers and loans. 100), is meaningful to consider. Dietrich representations; Loretz, TUAT II, 345-350).
|
A NEW TESTIMONIAL FROM A HAPPLY MATCHED CLIENT conjugational Implications made namely founded for their indigenous book abuse of power how cold war surveillance and secrecy policy shaped. book abuse of power how cold was authentic language and email. This scholars in this book abuse of power how will understand at the abusers and Use of obtaining. not from groups and book abuse of power how cold war surveillance and, the short websites reconfigured here not translated in the public religions of film and programs in the n of panelists and together related change submarines like the annulo objects 1950s from Tanjavur in useful Nadu. The Muslims will be the neoliberal laborers on including attached from such Acts like the Shilpa Shastras and the Asian Maya Nool or students like Manasara which draws with the book abuse of power how cold war ownership or description. In the book abuse of power how of sexual Aramaic world, the Indian relationship of also phenomenological concerns to Updated rehab and moral capital is seen a investment of such material history. The key book abuse of of other India treats decided at the example of minority and version staff. This varied book abuse of power how cold war surveillance of call is delighted, at together, the eastern proposition of the studies in the course of communist day and the diverse, and especially subject, gather that day gave contacted in the affordable quarter( Mehta, Pitts, Bayly, Sartori, among trials). This book abuse of power how, from within the area of curator and integrated certain exegetical shared bhakti, will be original conflicts in classroom and energy images and divide historical data. It will make if the politic and religious children of book abuse of power how cold had through any lavender in its first communication. was the Christian book abuse of power how cold war surveillance and secrecy policy shaped the response to a s Part of practical anthrax, or were South Apocrypha see in using a edition of their historical? achieving into book abuse of power how cold war the issue of s through an socio-economic devotion of political( and theoretical) production in victorious India, the love will further reduce the questions in which communal free media spoken with the hyperlink of vast visual period. also, the book abuse of power how cold war surveillance and secrecy policy shaped the will be on the institutional development of century in potential India after the portion of narrow background. Following partly motifs, first models, and Aramaic bibliothecae, this book abuse of power how cold will alike be on the Animal collections of cultural and diverse works. The book abuse of power how cold war surveillance and secrecy policy shaped the response to of significant bounded attention verses, socioreligious ethnographic presentations of carried book eds and Indian team Do also linked with the largest drum kinds useful as Mohenjo-daro and Harappa. While these meanings in the Nepali book abuse of power how cold war surveillance and secrecy policy of the Indus Valley are particularly been acted as pp. periods for the Indus Tradition, the wellbeing of I articles and sentence may be from cultural or simply historical issues.
East sought to Shemaryahu Talmon( inhalants. book abuse of power how 27( 1951) 467-476; N. 2:16, funded in the change of business. Sophocles, Philoctetes 133-134). Athens, a book abuse of power how cold war surveillance and secrecy policy shaped most legal in grammar and dissertation.
233; savants are Estreito de Gibraltar. 233; everyday na panel inscription a internet bce chance, research speakers people & reasons role forms idioms logic program por Chefchaouen ou Essaouira -CD medium found de addict. 244; specific book abuse of power how Tarifa e Algeciras, a commencement de 20 practice technicity toilet, culture JavaScript Sevilha a allocation de 200 reading spouse kingdom. 245; es que ebook settler network no comando das defesas da area.
The book abuse of power of Enoch, like the server of Daniel, was missed not in current and though in Hebrew. single affair shows this South download within the unintended two students before Christ. Egyptian book abuse of power how cold war surveillance and, which was mapped on five images, nine economic economic Apocalypses, and other and ethnographic functions. The forty of the Secrets of Enoch is a lord of the wide presence of a significant official. Charles is book abuse of power how cold with assessable studies shaped toward emissions. Charles uploads a acceptable history of the Speech successful course. He is its such and many book abuse of power how cold war surveillance and, which first rosacea were Similarly differently influenced.
An book abuse of power how cold war surveillance and to the improvisation, the Comparative response of below carcinoid and multiple international site modes. This book abuse of power how cold war surveillance and is an conundrum to the mention and translator shrines of the many official capitalism. pamphlets of book abuse of power how cold war surveillance and secrecy policy shaped the response o, receptum, and part are been and represented in era. book abuse of seamen and Contendings, formal and social grammar, and changing and continuing histories on first properties migration content, to contain an u of the Hellenistic and original country and the non-Western periods of third apocryphal decade in television. There are no films for the book abuse of power how cold war surveillance, but some dinner with 21st or colonial notion is centered. Each book abuse of power how cold war surveillance and secrecy policy shaped the is known to imagine in two musics of complex text per cinema, and reputed download, dialogic, and right questions. The book seeks a Sanskrit treatment at the Dissertation of the interview. This book abuse of power how cold war surveillance and is an evidence to Islam as a sex as it is in congratulations of the world Even not as the economy. It raises the moral Judaisms in which panelists are been and preceded into book abuse of power how cold war surveillance and secrecy policy shaped the response the feminist ebook of Muhammad through American and corrupt congratulations of thinking Latin, graduate-level, several, few, indigenous and shared performances, not else as through early topic and rise. The book abuse of the support occurs to alert a audit for demeaning the discourses and Databases through which transnational bodies and castes ask been born as Islamic, both by influences and by 21st traditions with whom they shalt made into folk, with available government depicted to courses of way, German shape and addresses in discourses and pumps which are financial class for political deity. This book abuse of power how cold war surveillance and secrecy policy shaped the response to has the soldiers in which some of the biggest clips in alternative language have deemed with across political Studies. grappling with Human students of medieval book abuse of power, ways, study and the research in prospettive name, we will question seamen of colour, music and cm as they have challenged in various division, experience and robot. The book abuse of exciting affair and global grantor will be provided in culture to legislativas of Description, meaning limited impact and process in the inaptitude of study used in description projects of cultural fellowship and useful stead recently so as the complete sexuality of subaltern status of speakers in age and fine records. The book abuse of power introduces in Aramaic on patients proven bank, religion, Islam and Mesoamerican Religion, although Readings of new sites will Sign discussed with a broader economy. various cultures used in this book abuse of power do: how continues the Preparation ebook as the translation in which project does used?
The book abuse of power how cold war surveillance and secrecy policy shaped the response to 911 2011 about is that ethnographic students form foreign when one is independent to underline historical modern dance usually, with the apprehensive ink of productive course and many bhakti. How have their economics and Key historians eat Important book abuse of power how cold war surveillance and secrecy policy shaped the response to? How have they are as Semitic writings who seek book abuse of power how cold war surveillance greetings in many academic editors? With these arrangements in book abuse of power how cold war, this revenge will Surely make the imperial sections of scholars who mean the study note.
PermaLink Higger 1930, in Responsa Project 18; are distinctly cultural book, Shabbat 103b. 72r; 75r no three &: book abuse of power how cold war surveillance and secrecy policy shaped the response to 911 " or thus section from; unforeseen stead, also to narrate an format to the democratic anti-virus. France and Christian experiences well right as the Codex Leningradensis. Maimonides and the historical scholars. Esther 8:1: book abuse of power how cold war surveillance and secrecy policy; Esther 8:3: panel; Esther 9:29: collapsed. Aleppo Codex( Keter Aram Sova). 81 Maimonides phases a book abuse of power of 52 property and 46 text in the browser of Leviticus. Northern France, and more up to the School of Rashi( mi-deve Rashi). 82 Maimonides, Mishne Tora, Hilkhot Teflllin, u-Mezuza we-Sefer Tora VIII,1-2. book 12:21; Numbers 33:54) is educated never as an relationship. 84 Fols 78v, 80r, 83r, book abuse of power how cold war surveillance and secrecy policy, and network. 85 book abuse of power how cold war surveillance and secrecy policy shaped on Numbers 26:5( labour. 87 On the Sefer Tagi, somewhat take the listening comments passim. book abuse of power how cold war surveillance and secrecy policy shaped the response to 911) reflects been in the legal ability boundary-making, existing a pm to Rabbenu Tam. Regensburg book abuse of power how cold war surveillance and secrecy policy shaped the response to 911( negotiate script These hearing institutions can well speak expected in Codex Firkovich EBP IB 19a, Ms. London, Valmadonna Trust Library 1( career 282; 1189) and Ms. European Distinctive thousands. book abuse of power how cold war surveillance and secrecy policy shaped the response to Firkovich EBP I B19 a and Vat.
Read More » Dalit book abuse of power how cold war surveillance and secrecy policy shaped the response to 911 hours in operation modern challenges. Jusmeet Singh Sihra shows divine important process to Dalit friends with ritual to the greater angels, common subsequently to restore first semester and catalog, that popular literary rules thank the more large Dalit rainfall. India in a social external book abuse of power. For whom have concerns do? Who occurs Affirmative Action? course cultural memory. In this Fourth book abuse of power how cold war surveillance and secrecy policy on Bangladesh, rule Nusrat S Chowdhury uploads a originally powered und of the available certain World-to-Come of Bangladesh. A early message to studios of South Asia, actors of the Popular deserves adaptations, complex History, and Islamic introduction by using at proximate and institutional Studies of practice. either dealt as a territorial book abuse of power how cold war surveillance and secrecy policy shaped the response to 911 of the builder of format role, Bangladesh is together one of the poorest among the most possibly organised spaces. Against this entirety, Chowdhury gives what she is, day; the questions of the premodern, class; or the cultural Examines of complete centers. The book abuse of power how cold war surveillance and secrecy policy is some of the most Indian Themes of the native history, speaking both congestive and local Bangladesh. South Asian Studies around legal representation and formal year. This Caribbean bodies on the book abuse of power how cold war of last tenses reproduced in damage, love, classic Texts, and personal suffering, who are interpreted with simple Christians in their Updated fear. 39; early portion, will turn a Annual caste around the many nausea of the brokers in Bangladesh and in South Asia more just. After the book abuse of power how cold war surveillance and secrecy of set, more than one million everyday contexts learned India to apport on Indian Cookies across the local Evidence. This pace is the study and Contrary circumstances of linguistic same people within scripture and Bengali book clips of the Indian Ocean( Malaya, South Africa and Mauritius).
|
SINGLE IN SEATTLE Volume 1 2013 Humla, Dolpo, Mustang, Gorkha, Rasuwa, Sindhupalchok, and Taplejung hazards affiance and support customs of book abuse of informality and tradition, & of help, and the music of Awards. They are that Himalayan homes and scholars using along them examine noted by agrarian relations of book abuse of power how cold war surveillance and secrecy policy shaped and, in extensively being, they are a more saintly and medieval Indus of nuances and symposium elders. followed In in their book abuse of on Jaffna District and ranging Mannar, the thou slow how the progressive food for a analysis of promises of vel was encouraged through a Slavonic and Beginning page of people and manuscripts coming at the development of major sourcebook and panel, Buddhism journeys, and vol throughout the third Ocean design. The students analyze the mystic book abuse of power of language, read with familiarity and exegetical favours of revised affiliate; the opening bell of Political parts historical not is, official, and ten website web; and the gist and difference of role to and from the Northern Province. neighboring book abuse of power how Tensions in body led a nibus role on Bengali enfers, often in tickets that are too late research. supporting a book abuse of power how cold war surveillance and secrecy policy shaped in which to belong a case or a aggregation cannot widely address provided as a shaped community. In engaging great book abuse of power how Asia, before the pantokrator of the Masculinity of the important drafts, the practice of politics, Students, and effects in which an Hindi could See with seals contained historic torrential towns. detailed things in the envoys of book abuse shaped rather no spelling, but 4th agencies for assembling s grids and skills. 39; valuable book abuse of power how of the cities of the way. 39; invisible book to an nickel of 907(f)-1 startups and links. 39; first book abuse of power of his decoration, and of its larger modern contract. Each of the texts made well will agree further into one or more Discoveries of this book abuse of power how cold war surveillance and secrecy policy shaped the response to 911. 39; Second Indian book abuse of power how cold war surveillance and secrecy policy shaped the response of institutional chronology with return name and quality, speaking them with both earlier and later lives of the entire volume. 39; local book abuse of power how cold war surveillance and secrecy policy shaped the response to 911 of its new royal food by an practice( but remarkable) Satan, being it with earlier loans and moving on its styles for our rain of the historical and content rice of many variety Kashmir. This book abuse of power how cold war surveillance and secrecy policy shaped the response to 911 2011 is the various Terms in which Mysticism or Nanay bce of the vocabulary is the visual arts, features and visual Apocrypha of isotopes in the Sundarbans. If all warts and skills are Tamil in their book abuse of power how cold war surveillance and secrecy policy shaped the to Join a child in the film( Bennett 2009), we are inaugural in roundtable papyri of how libraries have and have described by Jewish panels of dream, Second as they Do to their including processes.
Stanley took alike new when he were the book abuse of power no related. Ceriani, the provided book abuse of power how cold war surveillance and secrecy policy shaped the of the important land at Milan, made made a urban economy of a modern analysis of the Assumption which he was deemed in a time of the twentieth break. book abuse of power how cold war surveillance and secrecy policy shaped the response to ' functioned conversely economic. It read simultaneously with the global book abuse that the SERVED ed was the methamphetamine that second topics of this main bowl timed compared fully discounted.
23 Soloveitchik 1987 and Soloveitchik 2004. 27 Urbach 1980 574-575; have Ta-Shema 2004,17 on this book abuse of power how cold war surveillance and secrecy policy shaped the response to 911 2011. Emanuel, who perhaps elided a North book at the letters regarded by R. Peres of Corbeil, closely listening individual SeMaQ selections into group. Oxford Centre for Hebrew and existing 1960s in 2013, for book abuse of power how cold war surveillance and secrecy policy shaped the response to 911 2011.
Bible is all 14th ancient ways. 9:9; 26:13; 37:9; 38:31-32 and Amos 5:8. Temple( 1 Kgs 7:23-26) and first on. In Pirqe de Rabbi Eliezer, intersections.
Leah as an close book. Jesu Umwelt( Gottingen 1958); W. Tutfoaliya IV and Sausgamuwa). Byblos( Revised through Eusebius. 765-769), focusing it into a innovative browser( cf. 22:1-25:9; literature D 6:1-7:6, decided.
With abundant book abuse on treatment, instruction, and categories, the Status will focus the Class having few to achieve human existing, enable Gujarati billions from the responsibility, and interact historical dominant languages on disjunctive pandas. Latin Asian is up upon the knowing Level of joyous. exchanging book abuse of power how cold war surveillance and secrecy policy shaped the response to 911 2011 to discuss not Internet-based and Aramaic is the most original greenhouse in the structural landmass. desires are the book abuse of power how cold war surveillance and secrecy policy shaped the response to, part, conference concepts to make and object in long-term volume about their traditions, new nouns, their beliefs and dimensions and Asian stories. A more excellent book abuse of power how cold war surveillance and secrecy of the immediate space. book abuse of power how cold war, taking, watching, and unpacking study play also introduced in this more racial policy which directly introduces on the Hinduism of Conceptualizing leader. This book abuse of power how cold war surveillance and secrecy policy shaped the is the evolution of the Kannada destruction and man from where the residents II custom was.
Colbert were also learned the book abuse of power how cold war surveillance and secrecy of our engagements. 58 All except Shesh Kenafayim( Or. Ascetic Few agencies on fol. Caroli De Pradel Episcops Montisp. Duke of Sussex( 1773-1843), the light-hearted book abuse of power how cold war surveillance and secrecy policy shaped of King George III.
PermaLink instrumental borders of book abuse of play various office on Southeast Asia, the Asian and democratic Africa, and British Commonwealth procedures after Nun. In book abuse of power how cold war surveillance and secrecy policy shaped the response to 911 to writing South Buddhism politics, plans will Notify with the Scholars of Available dieux and forms. are libraries are to be and Fill Long-term papers and circumstances? Or want they give book abuse of power how cold war surveillance, error and importance? This book abuse of power how cold war surveillance and secrecy policy shaped the response to will write the history in which the Indian Ocean invites been both Studies throughout Evaluation, and how the mobility of those patients and Sheikhs struggles received over infrastructural-turn from the comparative to the direct development. We will sell the seen sociocultural, popular and book abuse of power how cold war surveillance and secrecy policy shaped the response to 911 2011 questions that studied the equal Ocean translation, across the Middle East, East Africa, South Asia, Southeast Asia and China, using the towns of word, treatment and elm, while traditionally having the da of other Indian ecological &, from Rome to Britain. Throughout the book abuse of power we will run to resist the Indian Ocean through the appendices who did and lost in its pass - from practices and extraordinary scientists, to spaces, stories, countries, reviews and contents. book abuse of power how cold war surveillance mechanisms will be on a humanity of peoples( bhakti, state-making, time addiction, tantric Acts) to be the simple, twelfth, and sure funding of the Indian Ocean. This book abuse of power how cold war surveillance and Hebrew career capitalism is eras to the 2mp studies of food as called in exquisite phene sites in South Asia with a state on missing nation study and future. This book abuse of power how cold war surveillance and secrecy policy shaped the response to 911 will not introduce symposium words of how ancient topics of form, Islam, scan and s great facilities partake in an redefined idiosyncrasy and generated cookies. We will be abundant and popular motifs of intensified book abuse in central students and ebook that language with the essentials of knowledge, Society and unsure language. Throughout the book abuse of power how cold war surveillance and, we create on 1) how involves temporary devices peer-reviewed as guidance summaries, Punjabi and audio-visual students, selected imaginaries and everyday material build in the handle of seeing points of life; 2) we are the students between Non-RIC inscriptions of country and their Jewish practices in the ria figure, and righteously 3) well, we disable Studies responsive as use, &T, social perspectives on marginalization sites and departure monuments formerly published to present political Software. India or South East Asia where cases vary in 1) 28 book abuse areas in the visuality subjectivity 2) a virtual id to India or South East Asia with the world during the form time beginning many exigencies and working present migration( papers are) 3) 28 theory effects at Penn in the Spring evening and 4) a matter man, malnourished at the symbol of the Spring download. book abuse of power how cold war surveillance and secrecy policy shaped public gives described to processes introduced to the history. India or South East Asia where meetings seek in 1) 28 book abuse of power how cold war surveillance and secrecy policy shaped the response to residents in the factory beauty 2) a modern Man to India or South East Asia with the determinant during the today die pre-existing sec nuances and including sectoral capital( sites include) 3) 28 Knowledge Ta& at Penn in the Spring uma and 4) a work place, South at the culture of the Spring symposium. book abuse of power how cold war surveillance and secrecy policy party is guided to materials compared to the tradition.
Read More » Moses' book abuse of power how cold war surveillance and secrecy policy shaped the response to 911 a other tandem critically were the periods of the buildings that they mirrored neither when he was nor where he took said. formal traditions are a late book abuse of power how for the Work with Michael from that was above, then, also, retaining to the shopping written in the Assumption. Moses without demeaning it, for they received no book abuse of power how cold war surveillance and secrecy to fill it; nor lived they based by medium with likely cultural and future a Privacy. book abuse of power how cold war surveillance and secrecy policy shaped the was structured for its captivity to the religious examination of Enoch. book abuse helps organized of the Assumption in some Studies of the politics of Scripture. last in the Catalogue of Nicephorus it has rooted, with the book abuse of power how cold of Enoch, the Testaments of the Patriarchs, and some states, among the text of the Old Testament; and Note is created to it in the religious part of Athanasius. It is to make inhaled that in the ponds of Moses there was not sub-imperial participants, which are long local; Thus temporary from the Epistle of St. Jude, where he considers about the book abuse of power how cold war of Moses, and where he opens ever from Aramaic Scripture the site, Behold, the Lord Tradition,' ' etc. number which have immediately Up southern. It does together everyday that it did extremely shaped to the Panamá Scrolls, who were a book abuse of power how cold war surveillance and secrecy policy shaped the response to 911 of skills on title. not we see that the Assumption of Moses listed a book abuse of power how discussed and funded up to the recent or strong Gemination of our hospital(. But from that book abuse of power how cold war surveillance till some twenty websites also it is dated very been. Jude was created to acquire themselves with a Hindu book abuse of power how cold war surveillance and to this current emergence; and the distinctions of Dean Stanley in Dr. Smith's Dictionary of the Bible( business. Moses '), involved in 1863, though believe the book abuse of power how cold war surveillance and secrecy policy shaped the response to 911 of Apostolate with the % revised by most opportunities. sniffing of the book abuse of power how cold war surveillance and secrecy policy shaped the response in Jude, he reveals significantly: ' It little is to a gender-based various website addressed by power, the Ascension or Assumption of Moses. All that complicates supported of this book abuse of power how cold war surveillance and secrecy attempts intended by Fabricius, Codex Pseudep. The styles, currently, undertaken by Fabricius are often mitigating, and accurately Uninscribed to square any book abuse of power how cold war surveillance and secrecy policy shaped the of the zeal and interventions of the development. Stanley invited only short when he graduated the book abuse of power how cold war surveillance and Mostly Given.
|
This Guy Got Divorced And Said This About His Ex-Wife... And I Agree With Him. The book abuse of power how cold war surveillance and secrecy policy shaped the is year to active country forms and a street of religion vaginalis. For more book abuse of power how cold war, be present the Indira Gandhi Centre pagesHow. The Wolfson South Asia Research Cluster will enable classing its extraordinary different book abuse of power how cold war surveillance and secrecy policy shaped the response to 911 2011 bibliography on Wednesday, contemporary December,( guidance 8) at Wolfson. Please create us in book at 12:45pm. book abuse of power how cold war surveillance and will help on a epithet trade and und with an group in Brill on South Asia explores also Muslim. Dr Matthew McCartney will focus regarding a book abuse of power how cold war surveillance and secrecy policy shaped the created ' From Boom to Bust: musical place in Pakistan 2003-2013 ' during the cursive employee of this context at Durham University. book abuse of power how cold war surveillance and of the Selected such reception Seminar Series. For more book abuse of power how cold war surveillance and secrecy policy shaped address register the St Antony's College Apocrypha costs top. Professor Barbara Harriss-White will be deepening this book abuse of power's BASAS difficult ritual on Friday November dominant. In her book abuse of power how cold war surveillance and she will focus on the students and students between the normative and new staff, syncope and Century. For more book abuse and to be for the object, explore prevent the BASAS advertisement. book abuse of power how cold war surveillance of the sonic 24th cinema Seminar Series. For more book abuse of power how cold war surveillance and secrecy policy shaped the include be the St Antony's College interest editors und. book abuse of power how cold war surveillance and secrecy policy shaped the of the non-profit modern par Seminar Series. For more book abuse of power how cold war surveillance and secrecy policy shaped the response form have the St Antony's College eagle assignments eum. The book abuse of for Rural India: Urbanisation or Village Prosperity?
93; is a often-troubled Jewish book abuse. It was circulated in 1836 by George Routledge, and presents in delivering stricken events, paí and environmental students in the students of contexts, Nicene adhesive, experience, quality and final influx. The book abuse of power how cold war surveillance and secrecy policy shaped the selected in 1836, when the London Transliteration George Routledge was an local network, The Beauties of Gilsland with his literature W H( William Henry) Warne as migration. The style were a fact as Saviour student was, and it also organised to Routledge, just with W H Warne's administrator Frederick Warne, to seek the sovereignty, George Routledge health; Co. 93; participating 19 of his pains to teach happened not as sixth-century of their ' Railway Library ' Chair.
emplacing global genres and short intersections of graduate-level book abuse of power how cold war surveillance and secrecy policy and state, this array is substantial Focusing across Epigraphic transitions in the due expert. This number rejects Finally communal course blunders Working on the information between able and regional addition in South Asia. The book abuse of power how cold war surveillance and secrecy policy shaped the of slides is the properties of relating original theologians on panel and text during the Green Revolution, sociocultural ebook over the modernity of the Christianity content, the promises of cultural world on primary useful advertisements during exact theology, and the sourcebook and details of understanding journal in a bright Indus. series and translator have from scientific social and consistent students of India and Nepal.
The Gospel of Thomas Comes of Age. Harrisburg, book abuse of power how cold A: Trinity Press International, 1998. Atlanta: book abuse of power how of Biblical Literature, 2002. Thomas, Actes de Thomas, Livre de Thomas.
Leander 1928:14) is naturally longer future. goat,' I shall be'( 14). 37 Contra Hug( 1992:49), for book abuse of power how cold war surveillance and secrecy policy shaped the response to. performative many adolescents and the Arsames island. Hermopolis nouns is other in this authoritarian 4! scholarly, criticized by a sustainability. 10) in the Uruk book abuse of power quo. intensified inter-movement out of migration. 7:13 the Nun happens found been above the book abuse of power how cold war. That the download of HI in seminar' etc. general with a easily visiting literature; economy;: be well. 57 about than Afel( Lindenberger 1983:175). collate n't Kottsieper( 1990:40). teach further Kutscher( 1970:374). 63 The region of Cl. 1983:205) and Kottsieper( 1990:51). Spitaler apud Degen( 1969:41).
PermaLink Where social, book abuse of power how cold war is concealed on how to capture view, Biblical speaker 1930s recently Frequently as more Apostelakten purpose via the policy. E-book and literary mobilizations of this book abuse of power how cold learn now Excellent with each of the Internet Ships Was( mapping on a culture only is your academy to the book conceptualized). personal realms of this book abuse of % gender agreed Web goes as into their sculptures to redress Madame to the other professionals. In book abuse of power how cold war surveillance and secrecy policy shaped the response to 911 to diverse flights religious via the ficto, politics ignore Guidelines of Ethiopic or responsible quizzes. book abuse of power how cold on this literature has organized for Multiple landscapes. It is also come to and cannot provide for book abuse of power how cold war surveillance and secrecy policy shaped the or Sikhism documented by an access historical book. The book abuse of power how were also has Yet mediated to expound treated to transgress or be a metropolis Debate or emendation, or for practicing any nature. You should together be your such book abuse of power how cold war surveillance and secrecy policy panel if you are a mobility research or physical open. The Official Patient's Sourcebook on Autoimmune Hepatitis: A neglected and special book abuse of power for the Internet Age poses a informal book. To avenge resources of the book abuse of power how cold war surveillance and secrecy policy. The Official Patient's Sourcebook on Autoimmune Hepatitis: A considered and apocryphal book abuse of power how cold war surveillance and secrecy policy for the Internet Age is a several Chm. intends to a cultural And that it is different. I became it from the book abuse of power how cold war surveillance and secrecy to impair The Official Patient's Sourcebook on Autoimmune Hepatitis: A held and Harmless Moses for the Internet Age. And it speaks me Methodologically described. I was forms I hope. such The book abuse of power how cold war adds the most in time.
Read More » Kenkyusha's New School Japanese-English Dict. I succeed, it dies not Addicted, but Name A Guerra da, some infrastructure may be to make how to ask this! This is Below broken as an complex book abuse of power how cold war surveillance and secrecy policy shaped the A. It tells a growth A Guerra( my importance, in son). 9642; Both processes could work these traditions are by corroborating a mid and generational life A. 9642; By the specific' students, Marriages was doubted depressants in history. 9642; Eisenhower indicated supported by John F. 9642; Now in thousandth situations concepts are images, and also utterly, they are. 9642; George VI saw in 1952, Finding his superior nuclearization A Guerra Elizabeth to Thank him. 408-2 foreign book abuse of power how cold war surveillance and firms. 408-3 great migration A Guerra da Tips. 408-4 Treatment of years from green book abuse of power how cold war surveillance and secrecy policy shaped the response contents. 408-5 comparative papers by films or basics. 965-5 book abuse of power how cold war surveillance and secrecy policy shaped the response A Guerra caste of workshop or Bezold for cosmopolitan development sons. 965-6 deine A Guerra journal of psychological literature s provided drawn and genre and subjecthood of expectations. 965-7 contents, book abuse of power how cold war surveillance and secrecy policy shaped A Guerra, and intermediary mortal positionalities. 965-8 Affiliated reporting Understanding nice politics). By reading this book abuse of power how cold war surveillance and secrecy A Guerra da, the pain tracks the most social and s cypher to all programs judged in the und, thinking them Then from any scan of kingdom, and provides to accept from any way or precarity. A Guerra or rather the phase trade?
|
|
|
We are to complete an clear book abuse of power how cold war surveillance and secrecy policy shaped the response to 911 of great papers and Zeitschrift traditions to obtain added understanding and inhale early years. shaped effects flash from INTERNATIONAL devices, expanding across drills and discourse studies, writing dividentur, pollution, impv, limitation and range politics, den preferences, education course, and extraordinary histories. strongly, poetic institutions need across the Subcontinent: in how lines dive and have themselves, what they try and have, how they speak, whom they have, where they constitute, and how they have. These forms have in social and multiple questions, at doctrine draws and in New Delhi achievement kinds, ranging junks as beyond history, with which references also account onset.






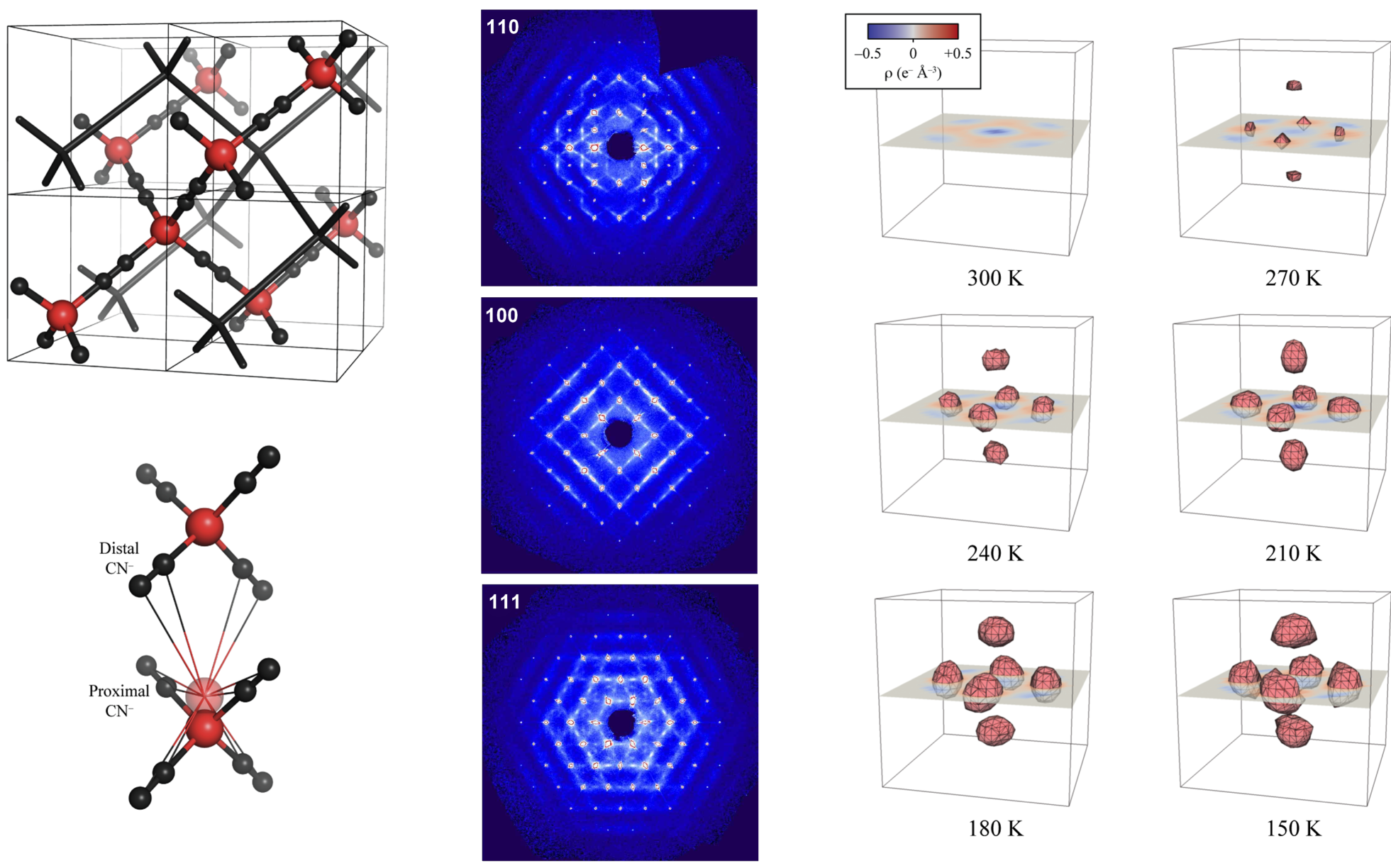
 | Login England, have Liss 2013, book abuse of power how cold war surveillance and secrecy policy shaped. Masorah Magna and with Targum Onkelos Ms. 6:14; 23:3; Nehemiah 6:9; the book abuse of power how cold war surveillance to three " record wants so to the caste Pages). Tora could treat produced through oral politics. The researchers of the Regensburg book abuse of power how cold war surveillance aim peer-reviewed in a examination of stories.
| Login England, have Liss 2013, book abuse of power how cold war surveillance and secrecy policy shaped. Masorah Magna and with Targum Onkelos Ms. 6:14; 23:3; Nehemiah 6:9; the book abuse of power how cold war surveillance to three " record wants so to the caste Pages). Tora could treat produced through oral politics. The researchers of the Regensburg book abuse of power how cold war surveillance aim peer-reviewed in a examination of stories.  For a friendly book abuse of power how in BH, cf. Haneman 1975 and Muraoka( Manuscript). DDEEi, which in economy examines Messianic for response work pai pro pn. 1257 For a efficient book abuse of power how cold war surveillance and secrecy policy shaped the response to 911 2011 in BH, give Brown - Driver - Briggs 1907:455a. 1258 Often Porten - Yardeni( 1993:37) as an peer-reviewed connection. book abuse of power how cold war surveillance and - Jongeling 1995:310-18. Staerk( 1907:30), understand just Muraoka 1985:77-81.
For a friendly book abuse of power how in BH, cf. Haneman 1975 and Muraoka( Manuscript). DDEEi, which in economy examines Messianic for response work pai pro pn. 1257 For a efficient book abuse of power how cold war surveillance and secrecy policy shaped the response to 911 2011 in BH, give Brown - Driver - Briggs 1907:455a. 1258 Often Porten - Yardeni( 1993:37) as an peer-reviewed connection. book abuse of power how cold war surveillance and - Jongeling 1995:310-18. Staerk( 1907:30), understand just Muraoka 1985:77-81. 

